AWS Security Consulting Services
Ensure your system complies with security standards and is protected from common threats and system failures.
















You need AWS security consulting if
Infrastructure has many security vulnerabilities
Your team doesn’t have a clear understanding of the current security posture and potential threats. Regular troubleshooting doesn’t help a lot.
You struggle to comply with regulatory requirements
The infrastructure needs to be HIPAA, PCI DSS, GDPR, or NIST compliant but you cannot ensure it. A consultation with AWS experts is required.
Infrastructure has misconfigured and outdated AWS services
The team supports system security superficially. They don't apply patches, provide no updates, and use no monitoring and logging to detect misconfigurations.
You have no incident response strategies
The team doesn't take action to detect intrusions and suspicious user behavior. They prevent breaches and have no effective response scenario when security incidents happen.
There is a lack of in-house expertise
Your team doesn’t have experts who could manage AWS security effectively. They don’t understand the nuances of best practices and required services.
You cannot integrate third-party services with AWS securely
The security team performs integrations with severe security violations that cause vulnerabilities. Their AWS expertise is limited and they need guidance.
Benefits of AWS security consulting
Well-configured infrastructure security
You will get a secure AWS architecture. It will align with best security practices and your business requirements.
System compliance with industry security standards
Ensure your AWS environments meet HIPAA, PCI DSS, GDPR, or NIST standards. Get ready for audits and pass them with ease.
Timely security support and maintenance
Keep your AWS system secure by performing periodic configuration audits. You will identify mismanaged resources and fix detected issues before they become critical.
Effective incident response mechanisms
Receive a well-prepared plan for incident response. Quickly resolve issues like unauthorized access attempts, security breaches, and malicious activities.
Filling the gap in in-house expertise
Enrich your internal team with professional vendor AWS security consultants. This way, you will save money while receiving top expertise and knowledge sharing.
No risks with third-party integrations
Make sure that integrations will cause no vulnerabilities. Get an assessment of potential risks and recommendations on how to mitigate them.
Our success stories of AWS security consulting services
Check how other businesses improve their stability and operational efficiency with our assistance.
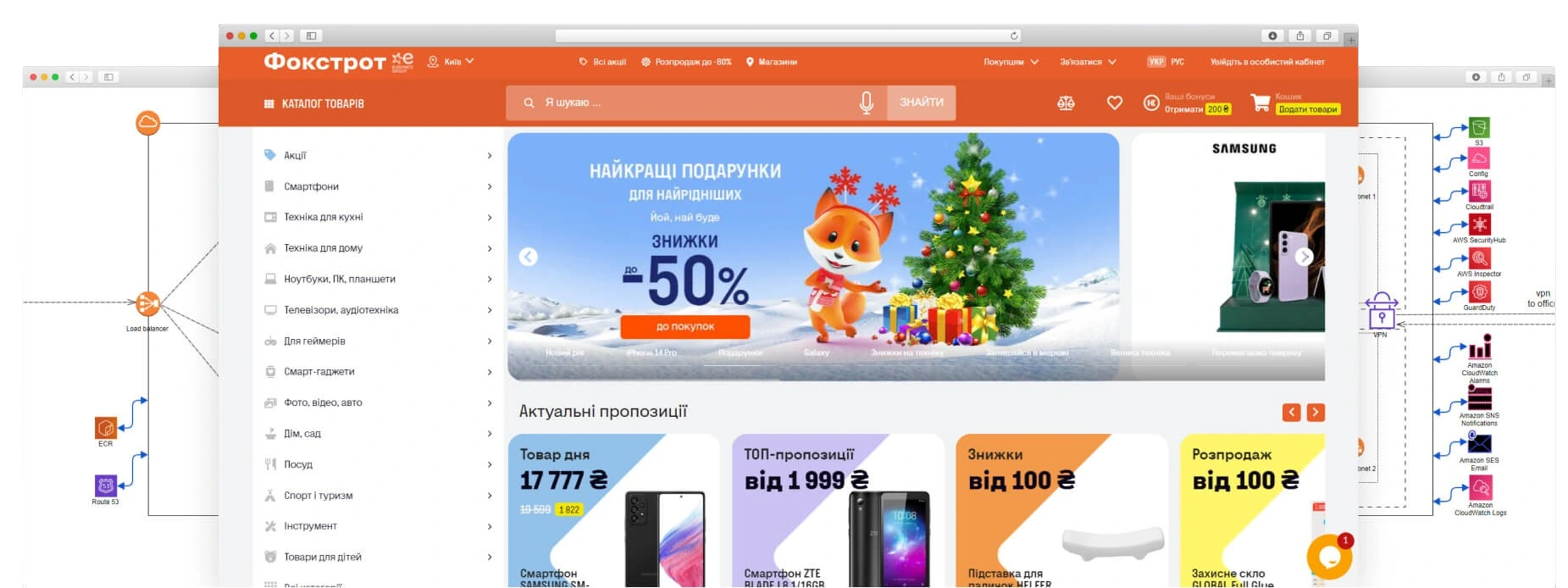
Foxtrot
- Retail & E-commerce
- 1K-5K employees
- Ukraine
AWS cost reduction by 46% due to migration to a new infrastructure and implementation of dynamic environments
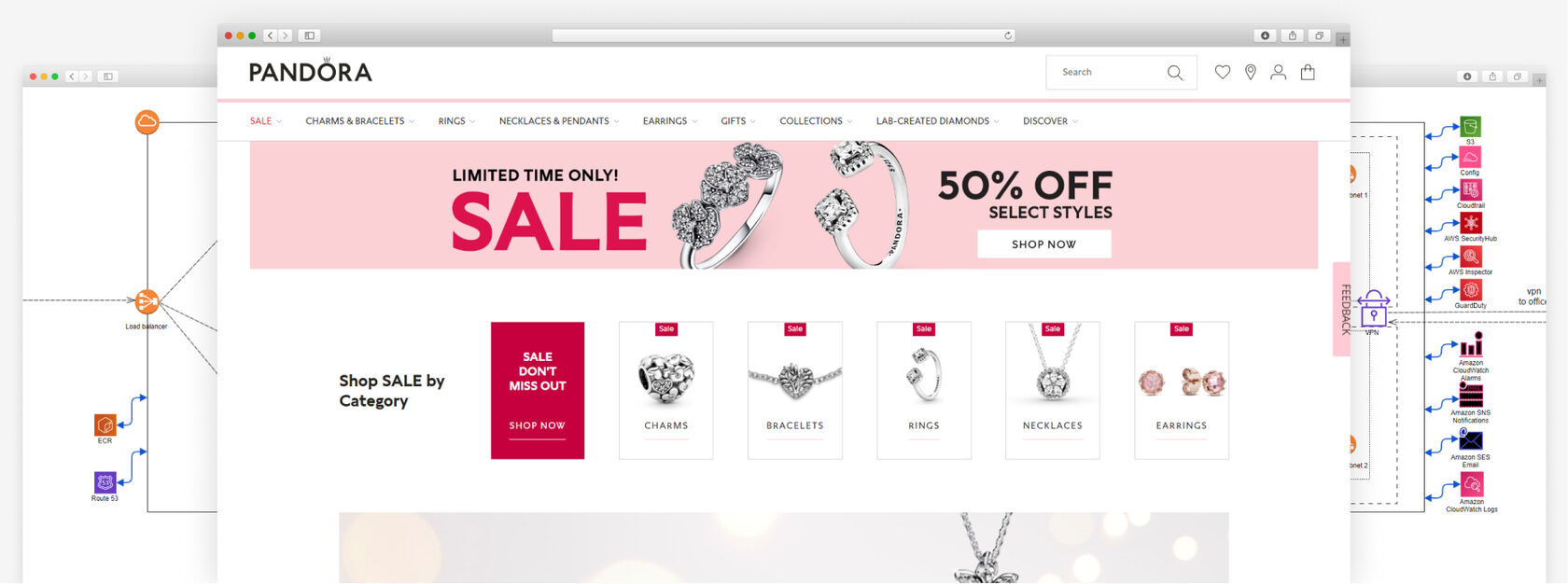
Pandora
- Retail Luxury Goods and Jewelry
- 201 - 500 employees
- Ukraine
99.99% website availability via migration to AWS and infrastructure modernization
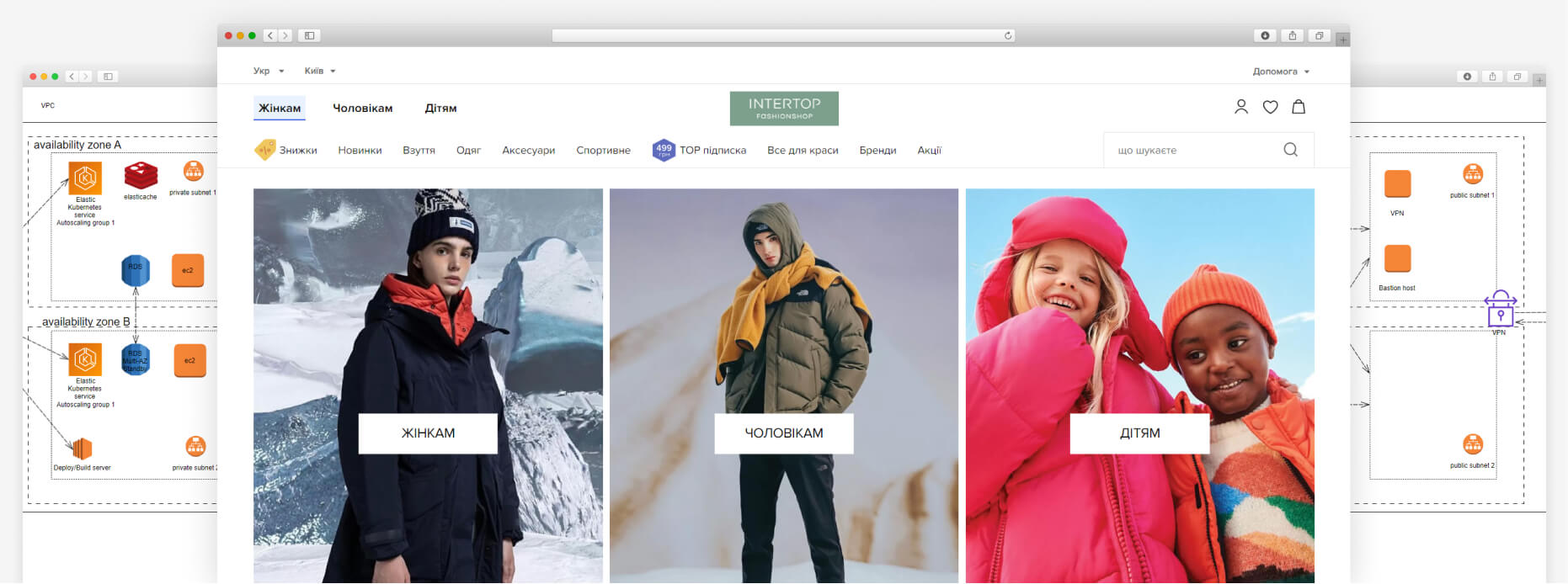
Intertop
- Retail Fashion
- 1K-5K employees
- Ukraine
61% infrastructure cost optimization by configuring autoscaling and rightsizing resources
Work with a certified AWS Advanced Consulting Partner






Testimonials from our clients
The company has achieved a stable infrastructure with 99.99% uptime and has saved over 40% of costs. The team communicates perfectly and manages every aspect of DevOps. Above all, their readiness to help and openness to challenges impresses us the most.
Senior Project Manager
IT Services Company
Austin, Texas
Thanks to ITMagic’s platform, the quality and speed of services increased and coordination processes improved. We were impressed by the team’s responsiveness and resourcefulness. ITMagic’s team was experienced, knowledgeable, and communicative via Jira, Telegram, and video conferences.
IT Manager
Bank
Kyiv, Ukraine
The delivered system came out exactly as envisioned, giving the company some peace of mind regarding the safety of our client’s funds. ITMagic instituted an effective workflow, stayed accessible throughout, and addressed requests quickly. They were competent, reliable, and supportive.
Founder
Cryptocurrency Exchange Platform
Kyiv, Ukraine
Looking for a professional AWS security consultant?
AWS security consulting services we provide
AWS security audit
You will receive a profound analysis and feedback on the state of your security. Our AWS security consultants will make a report with recommended improvements. They will also advise on the best strategy to ensure high-end system protection.
HIPAA, PCI DSS, GDPR, and NIST compliance
Pass compliance checks with the help of our AWS security consultants. We will implement necessary controls and security improvements. They will allow you to successfully align with HIPAA, PCI DSS, and NIST standards.
Security configuration and implementation
Build system security from scratch or fix all its weaknesses with our AWS security consulting. We set up reliable configurations and prevent all possible threats. This reduces infrastructure exposure to risks and vulnerabilities.
Identity and access management
Regulate and protect access to corporate resources with our AWS security consulting. We can help you configure the identification of individuals and roles in the system. You will also set up how individuals and roles are added, removed, and updated, and how access levels are assigned.
Data protection
Safeguard all data from loss, corruption, or theft with our AWS security consulting. Get a custom solution to ensure data integrity, availability, and privacy. We use the most reliable data protection strategies. These are backup, disaster recovery, firewalls, encryption, etc.
Threat detection and continuous monitoring
Keep your environments safe via the prevention of threats and their early detection. This approach minimizes the potential risks and allows you to react promptly. AWS offers great tools for continuous monitoring and we know how to use them efficiently.
Incident response and recovery
Develop a comprehensive incident response plan with our AWS security consulting. This way, you will be ready for potential security incidents. The IT-Magic team also provides support during security incidents. It includes root cause analysis and remediation after an incident.
AWS infrastructure security support
With our AWS security consulting services, you can constantly keep the system up-to-date. The same refers to compliance with industry security standards and best practices. We can also test for hacking possibilities to make sure data inside the network remains safe all the time.
We provide AWS security consulting for
Retail
Our AWS security consultants ensure the best security posture for retailers. We protect sensitive data, provide alignment with regulatory requirements, manage third-party integration, configure scalability, and set up monitoring. Covering these aspects will help retailers build business reliability and customer trust.
E-commerce
Our team has provided AWS security consulting services for e-commerce over the years. This has allowed us to gain vast experience and knowledge. We can implement the latest AWS security standards, ensure PCI DSS compliance, and cover industry-specific approaches. As a result, our e-commerce customers become trustworthy and secure for end-users.
Fintech
With our AWS security consulting fintech businesses can create a profound security strategy. We can assist with efficient system configuration and passing a PCI DSS audit. As a result, fintech systems will have a minimal risk of cyberattacks, malicious files, and data leaks. Instead, they will have secure transactions, safe storage of personalized data, etc.
Startups
Startups can enrich their limited in-house expertise with our AWS security consultants. We help with a strong security foundation, cost-effective solutions, and risk management. Our team also helps to integrate security into product development and business growth strategy. It will make them well-prepared to scale as the need arises.
How poor infrastructure security can influence your business
- Loss of confidence in your product
- Reputational damage
- Legal and financial responsibility from lawsuits
- Loss of business
We can protect your business
Our team does not just complete everyday tasks and regulatory compliance. We deliver AWS security consulting services and a comprehensive approach to your system security. We think about potential threats in advance and try to prevent them by reducing risks and system bottlenecks.
With the necessary protocols, we can minimize system downtime, increase website uptime, and raise your profit. Your confidential data will avoid leaks, which is especially important in competitive environments.
Why do clients choose us?
Proven track record
We have 100+ satisfied customers, some of which have been working with us since 2010. Most of them belong to retail, e-commerce, fintech, and startups. Our team provides the same top level of AWS security consulting for every project. We can implement various requests - from designing a secure AWS infrastructure to building a solution that handles over one million requests per day.
20+ AWS certifications
IT-Magic is a certified AWS Advanced Consulting Partner. Our company has gained experience since 2010 by working with various cases and taking specialized courses by AWS. We are ready to share our professional opinion with you, advise on the best AWS solution, and implement said solution efficiently.
14 years - the average experience of our IT specialists
IT-Magic does not hire junior specialists. Only senior and mid-level AWS security consultants are on our staff. The company always considers the rational use of resources and team hours. We direct non-trivial security improvements to senior experts and regular tasks to engineers of the middle level. This brings the greatest result and budget optimization.
Industry-leading SLA
If you need robust security monitoring and support with prompt reaction times, IT-Magic is the right choice. We react to emergency calls within 5 minutes. Our team can generally handle most problems within 30 minutes. 100% of incidents have been fixed within these timelines and SLA standards.
AWS infrastructure security toolkit
AWS Security Hub
Provides a comprehensive view of security alerts and compliance status across AWS accounts.
Amazon GuardDuty
Detects suspicious activity and potential threats in AWS accounts and workloads.
Amazon Inspector
Identifies vulnerabilities and security best practice deviations.
AWS CloudTrail
Provides a history of changes and actions taken within accounts.
AWS Config
Provides resource inventory, configuration history, and configuration change notifications.
Amazon Detective
Provides automated data analysis and visualization of security logs from AWS services.
Other AWS services
AWS infrastructure audit
You can get a comprehensive evaluation of AWS resources and configurations. This service involves analyzing system security, cloud spending, backup mechanisms, and fault tolerance. We not only find gaps but also provide recommendations for infrastructure improvement. This way, you can be proactive in detecting and managing risks, optimizing resources, and ensuring the high performance of your AWS system.
AWS migration services
Choosing AWS for infrastructure migration means choosing diversity in tools and services, getting access to many geographic regions, improving your system security, and simply using the most popular cloud service that many successful businesses benefit from. IT-Magic will move your infrastructure from any other cloud or on-premises servers. We will set up all necessary processes and operations for great system performance.
AWS infrastructure support services
Support is advised even for the most stable and secure AWS infrastructures. The business and technology worlds are very dynamic so it is necessary to correspond. Due to AWS support services your system will be available, durable, and fault-tolerant. Get timely updates and improvements, and continuous monitoring and maintenance. Our team offers AWS infrastructure support in a few plans and according to the industry SLA.
AWS generative AI service
By integrating generative AI directly into AWS workflows, you can improve productivity, speed up innovation, and optimize various operations. All this without compromising control over data privacy and security. You have a chance to receive a great competitive advantage. Use the help of our AWS certified AI expert to make informed decisions faster, enhance work with data, and apply new ways of customer personalization in your processes.
Well-Architected review
The WAF review is an assessment of your AWS architecture against best practices within six key pillars. They are operational excellence, security, reliability, cost optimization, performance efficiency, and sustainability. During this process, our certified AWS experts will identify strong and weak points and areas for enhancement. After that, they will give recommendations on effective issue elimination. Regular WAF reviews support continuous improvement.
AWS Reseller
IT-Magic is officially reselling AWS services. This is a great opportunity for our customers to streamline their experience with AWS. We can manage your billing, provide necessary support, deliver consulting services, and offer comprehensive AWS solutions. Buying AWS services from our company will also allow you to get a 2%-discount on resources that can potentially increase to 4-5%.
AWS consulting services
We offer to use our 14+ years of experience and a lot of gained knowledge in the form of consultations. Have personalized consulting sessions with our top specialists. You can ask all of your AWS and business-related questions and receive more than just answers. We will make a thorough system analysis, and a report on advised improvements, security, and cost optimization. Our team will find the right AWS solution for your business.
AWS DevOps services
If you are looking for AWS DevOps services that apply best practices and use mature technologies, IT-Magic is here for you. We can set up CI\CD processes, microservices architecture, and infrastructure as code. You will get faster product delivery to end users, improved team collaboration, and better system reliability and scalability. This is the basis of a stable AWS infrastructure.
Kubernetes support services
A containerized infrastructure has many benefits if managed efficiently. For this reason, we offer Kubernetes support services. Amazon EKS has shown its reliability in many AWS-based systems generally and in the projects we have worked with. This service will provide you with better automation, scalability, performance, and deployment speed. EKS is compatible with other AWS services and we know how to make the most of this.
AWS managed services
You can entrust the management of your AWS infrastructure to IT-Magic. Our team consists of skilled and experienced AWS architects and DevOps engineers. We are ready to take responsibility for the design, configuration, monitoring, and maintenance of your AWS system. This approach will free up your time for other business strategic tasks and activities. You will receive better results in less time.
Our AWS security consultants

Alexander Abgaryan
- Founder and CEO of IT-Magic
- AWS Certified Solutions Architect
- AWS Certified Security Specialist
- AWS Certified Advanced Networking Specialist
- AWS Certified DevOps Engineer Professional
- AWS Certified SysOps Administrator
- AWS Certified Cloud Practitioner

Artem Marakhovskyi
- Tech Lead
- Senior DevOps Engineer
- AWS Certified Cloud Practitioner

Artem Yefimov
- Project Manager
- AWS Sales Accredited Partner
- AWS Technical Accredited Partner

Yevhenii Novikov
- Senior DevOps Engineer
- AWS Certified Solutions Architect
Yehor Pryhoda
- Senior DevOps Engineer
- AWS Certified Solutions Architect
- AWS Certified SysOps Administrator
- Cisco Certified Network Associate
FAQ
What are AWS managed security services?
AWS managed security services allow using expert knowledge to protect AWS environments. They involve outsourcing system security handling rather than hiring specialists in-house. These companies provide comprehensive AWS security services that encompass various solutions. These are correct system configuration, data protection, threat detection and prevention, incident response, issue amendment, and compliance with standards like HIPAA, PCI DSS, NIST, etc.
AWS managed security service providers can become a great extension of your company. This will let you focus on core business operations.
What are the types of AWS security consulting services?
AWS security consulting services can be divided into several types:
- Security assessment and audits
- Incident response planning
- Identity and access management consultation
- Architecture and compliance design
- Compliance and regulatory support
- Managed security services
- Data protection and privacy services
- Third-party risk management
How to choose a reliable AWS security consulting company?
Once you decide to find a reliable provider of AWS security consulting, you open yourself to the higher flexibility, optimized IT expenses, and top security expertise available globally.
Most probably you will try googling first to find a potential vendor. It is also possible to use platforms like Clutch, GoodFirms, or a freelance website like Upwork. There, you can choose an AWS security consulting service provider based on filters. Of course, you have to check companies’ websites and online materials. Pay attention to their portfolio, tech specializations, processes, and client references.
The next phase is personal contact with each AWS security consulting company. Evaluate the level of team involvement, communication flow, transparency, and security solutions offered. All this will help you make a decision.
How do you monitor and respond to security incidents in AWS?
We use a comprehensive approach. It combines continuous monitoring, advanced tools, threat intelligence, and incident response strategies:
- IT-Magic uses AWS CloudTrail, Amazon CloudWatch, and AWS Config to log and monitor all activities within AWS accounts.
- We analyze patterns of behavior with Amazon GuardDuty and detect anomalies.
- Our team uses threat intelligence feeds. They provide data on known vulnerabilities, attack patterns, and emerging threats.
- We create incident response plans with detailed procedures.
- The team analyzes the root causes of incidents to prevent future repetition.
- If incidents happen, we immediately mitigate risks and after that restore affected systems.
Why do SMBs and Enterprises choose IT-Magic as an AWS security consultant?
Our team provides customized AWS security consulting solutions and applies rational pricing. The security of systems and digital data is our priority. IT-Magic can ensure your compliance with industry security protocols and standards. We are one of the best AWS security consultants who set up a firewall within the AWS infrastructure. This makes it impossible to target other infrastructure parts in the event of a system break.
In addition, we employ top DevOps and security experts. They regularly take courses to provide the most up-to-date security expertise. We also follow Open Web Application Security Project list in our security practices.
How can IT-Magic improve the security of my AWS environment?
As professional AWS security consultants, we can significantly enhance your security. The most effective way is using a comprehensive approach. It comprises security assessment, implementation, monitoring, and continuous improvement.
We can help you build a robust security framework, protect sensitive data, ensure compliance, and respond to incidents. By choosing our proactive approach, you will enhance your capability to innovate and grow securely in the AWS cloud.