For fintech companies, PCI compliance tends to show up at awkward moments.
A payment partner asks about it during onboarding. A large prospect brings it up in procurement. An investor wants to know whether security controls are mature enough for the next stage of growth. Suddenly, a topic that seemed technical becomes a business blocker.
That is why how to become PCI compliant is not just a question for security teams. It matters to leadership, product, operations, and anyone responsible for keeping growth from stalling.
There is also a common misunderstanding at the start. Teams move to AWS and assume the cloud has already solved most of the problem. It has not. AWS gives you a solid infrastructure base, but PCI compliance still depends on how your own environment is built, who has access, where payment data travels, what gets logged, and whether your team can show that controls are working in practice. The AWS shared responsibility model explains that separation clearly, and the PCI Security Standards Council makes it clear that PCI DSS is about protecting cardholder data and the systems that can affect it.
That may sound like a lot. In some ways, it is. Still, most fintech teams do not fail because PCI is impossible. They struggle because the work starts too late, the scope is too wide, or the environment was never designed with compliance in mind.
The better path is usually simpler than people expect. First, figure out what is actually in scope. Then isolate it. Then build controls and evidence around that smaller environment. That sequence is not flashy, but it works.
Start with PCI scope, not tools
The first real PCI decision is not about services, scanners, or dashboards. It is about boundaries.
Before you choose tools, you need a clear view of your cardholder data environment. In plain terms, that means identifying where cardholder data is stored, processed, or transmitted. It also means identifying the systems around it that could affect its security.
That second part gets missed all the time.
A team may know where payments are processed, but not realize that a support workflow, an admin utility, a shared logging path, or a reporting integration quietly pulls more systems into scope. On paper, the payment service looks small. In practice, the environment around it is sprawling.
This is where PCI starts getting expensive.
If payment data touches too much of your platform, then more of your platform has to be controlled, reviewed, documented, and defended. The cost is not only technical. Audit preparation gets harder. Ownership gets blurry. Evidence lives in too many places. Small changes take longer because more people and more systems are involved.
A narrower scope changes that picture fast.
When the systems that truly need to handle payment data are isolated from everything else, compliance becomes easier to reason about. Security improves too, but so does the operating model. Reviews are smaller. Access is easier to manage. Logging is cleaner. Assessment conversations are more straightforward.
That is why scope reduction should be treated as a design goal, not a cleanup project for later.
A simple way to frame it is this:
- If your whole platform touches payment data, PCI becomes a drag on everything.
- If only a tightly controlled part of the platform handles it, the work stays contained.
That is not a small difference. It shapes the whole project.
Understand what AWS covers and what your team still owns
This is the part many teams think they understand until they begin preparing for an assessment.
AWS is responsible for the security of the cloud. Your company is responsible for security in the cloud.
It sounds like a slogan until you start unpacking it.
AWS handles the physical infrastructure, the facilities, the underlying hardware, and the foundational service layer that supports the cloud platform. Your company still owns the way its environment is configured and operated. That includes access control, network design, application configuration, patching, encryption choices, logging, monitoring, procedures, and day-to-day governance.
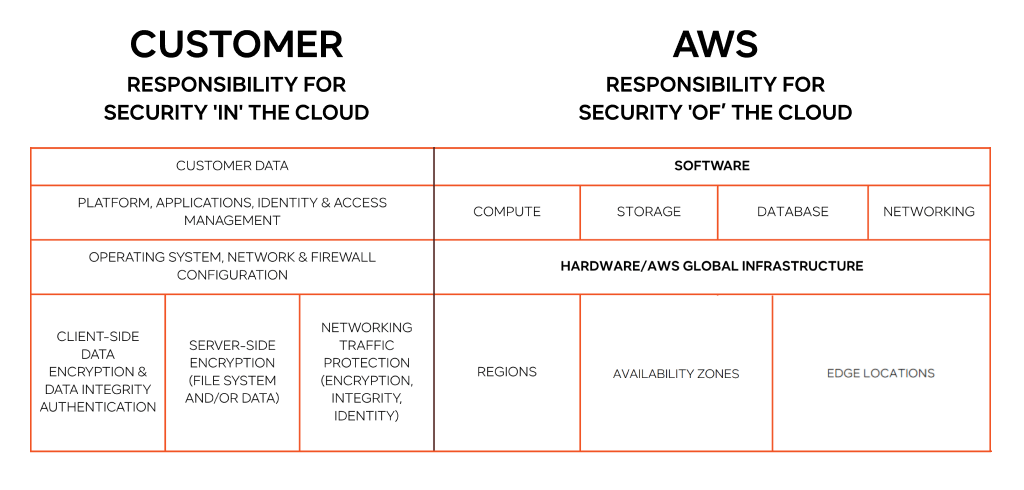
So no, using AWS does not make a fintech automatically PCI compliant.
It helps. It gives you reliable building blocks. It gives you documentation and services that support a strong security program. But it does not remove your responsibility for the final environment.
That distinction matters because teams sometimes assume that “running on AWS” and “being audit-ready” are nearly the same thing. They are not.
A cloud environment can still be messy. It can still have weak access controls, over-permissioned users, shared resources that widen scope, inconsistent monitoring, or policies that exist only in theory. None of that disappears because the infrastructure is hosted by a trusted cloud provider.
A simple ownership view looks like this:
| Area | AWS helps cover | Your team still owns |
| Physical datacenters and core infrastructure | Yes | No |
| Managed service infrastructure | Yes | Partly, depending on service model |
| IAM design and access policies | No | Yes |
| Security groups, routing, segmentation | No | Yes |
| Guest OS and app patching on EC2 | No | Yes |
| Data classification and retention | No | Yes |
| Encryption choices and key access | Shared | Yes |
| Logging, monitoring, alerting, review | Shared tools | Yes |
| Policies, procedures, evidence, audit readiness | No | Yes |
For leadership teams, this is an important mindset shift. Moving to AWS reduces infrastructure burden. It does not outsource accountability.
What a PCI-ready AWS environment should include
A strong PCI-ready environment is usually more disciplined than complex.
It does not need every security tool available. It does need clear control over the systems that matter.
Clear separation between payment systems and everything else
The less connected your payment-related workloads are to unrelated services, the better. In practice, that often means separate AWS accounts, restricted network paths, limited administrative access, and strong boundaries between in-scope and out-of-scope workloads.
This is one of those areas where architecture decisions pay off for years. If the environment is designed with separation in mind from the beginning, almost every downstream compliance task gets easier.
Tighter identity and access management
Many PCI problems are really access problems in disguise.
A company may have a decent network layout and solid logging, but if too many users have broad permissions, the environment is still weak. The same is true if shared credentials exist, if privileged access is loosely controlled, or if administrative users are not reviewed regularly.
A practical PCI environment should lean on:
- least-privilege access
- multi-factor authentication
- strong control of privileged roles
- fast removal of outdated permissions
- routine access reviews
- limited paths into production systems
These are not “nice to have” items. They are central.
Sensible encryption and key handling
Encryption is expected. The hard part is usually not turning it on. The hard part is operating it well.
Who can access keys?
How are secrets stored?
What happens when credentials need to rotate?
Are sensitive values leaking into logs, exports, or backups?
Those are the kinds of details that separate a control that exists on paper from one that actually holds up.
Logging that people can actually use
Logging is only helpful if it tells a clear story.
A PCI environment should make it easy to answer basic questions: who accessed a system, what changed, when it happened, and whether anyone reviewed it. If logs are spread across too many tools, accounts, or teams, that story becomes harder to reconstruct.
Good logging is not just about retention. It is about visibility, ownership, and review.
A repeatable approach to patching and vulnerabilities
Some teams still handle patching as a loose operational habit. That does not hold up well in a PCI context.
The environment needs a pattern for vulnerability review, remediation, escalation, and exception handling. Otherwise, issues accumulate quietly until they become audit problems or security problems, and often both.
A real incident response path
Every company says it would respond quickly to a security issue. Fewer companies can describe exactly how.
For systems in or around the CDE, response should not depend on improvisation. Roles should be clear. Escalation should be defined. Evidence handling should already be understood. When an incident happens, that is not the time to decide where logs are or who owns the decision-making.
_______________________________________________________________________
Looking to make your existing system PCI DSS compliant and got lost in the process?
Pause and review the architecture before compliance work gets more expensive. IT-Magic can help you evaluate where the design is helping and where it is getting in the way.
_______________________________________________________________________
Compliance is also an operational process
This is the part that catches fast-moving fintechs off guard.
They expect the hard part to be technical. A lot of the time, the harder part is operational.
It is one thing to have a control. It is another thing to prove that the control is defined, assigned, performed, reviewed, and documented on an ongoing basis.
That means PCI is not only about architecture. It is also about habits.
Take access reviews as an example. A team may say that privileged access is reviewed regularly. Fine. But who does the review? How often? Where is it recorded? What happens if someone keeps access they no longer need? Can anyone show the evidence without digging through email and chat?
That pattern shows up again and again.
The same happens with change management. A company may say that production changes are approved. But when asked for proof, the process turns out to be informal, inconsistent, or dependent on a few people remembering to leave comments in the right place.
None of this is unusual. It is common. But it slows audits down because the problem is not always the absence of a control. Often the problem is that the evidence is incomplete or hard to collect.
This is why the smartest teams do not treat evidence gathering as a last-minute task. They build it into normal operations.
If an access review happens, record it then.
If a change is approved, make the approval traceable.
If an exception exists, make ownership clear.
If a policy matters, make sure people know where it lives and who maintains it.
That kind of discipline may feel slower in the short term. In reality, it keeps the project from turning into a scramble later.
A practical roadmap to PCI compliance on AWS
There is no single universal playbook, but the sequence below works well for many fintech teams.
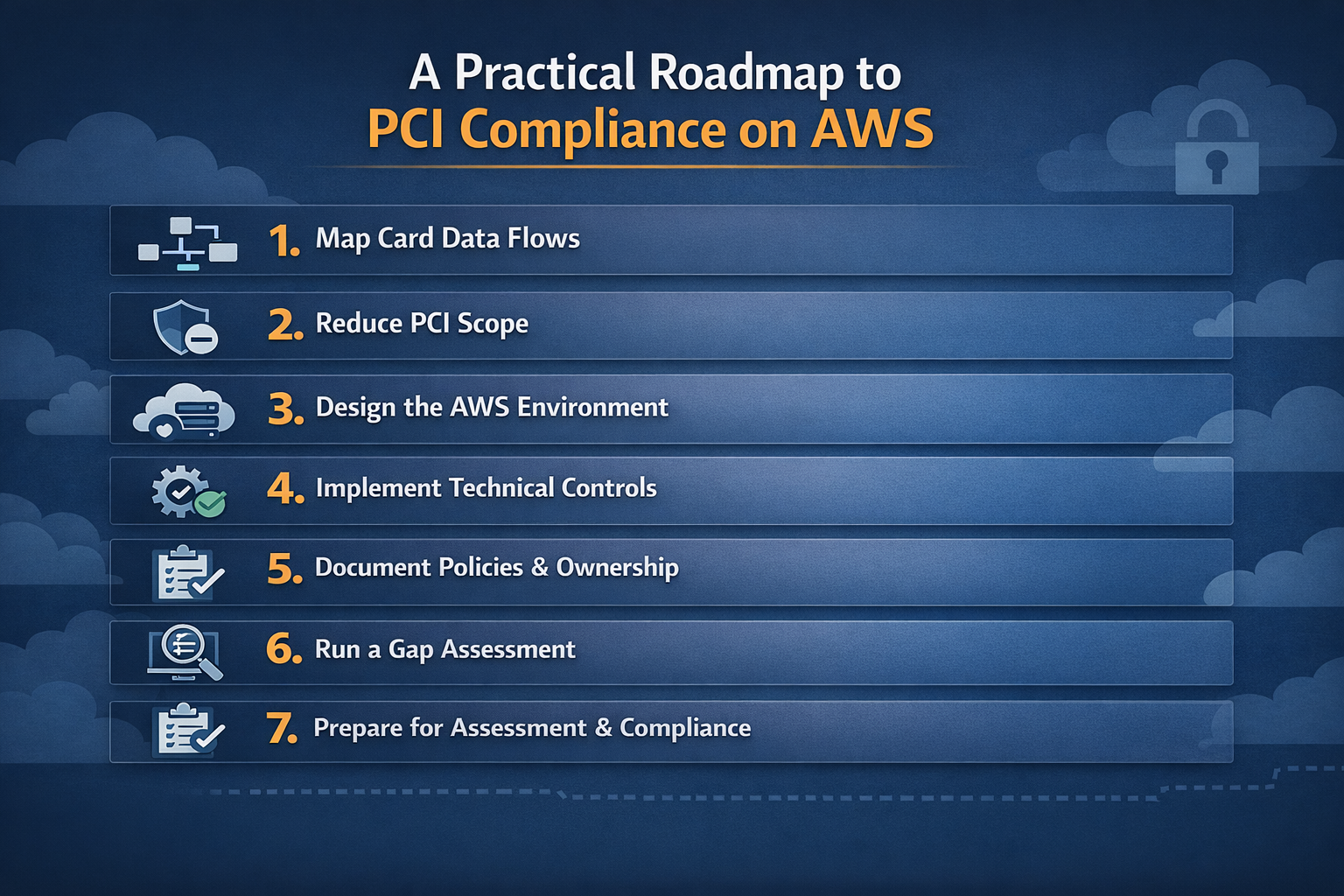
1. Map card data flows
Start with the facts.
Where does cardholder data enter the system?
Where does it go next?
Does it get stored?
Which third parties are involved?
What internal tools can touch it?
Do support, analytics, or export workflows interact with it in any way?
Do not stop at the obvious payment path. The messy parts are often off to the side.
2. Reduce PCI scope
Once the flows are visible, start removing what should not be there.
Sometimes this means stopping unnecessary storage. Sometimes it means redesigning a support tool. Sometimes it means ensuring that logs never capture data they do not need. In other cases, it means separating a service that had no business sitting close to payment handling in the first place.
This is often the highest-value step in the whole process.
3. Design the AWS environment around the CDE
Now build the environment to reflect the scope you actually want.
That usually means stronger boundaries, fewer shared paths, cleaner separation of duties, and tighter control over how administrative actions happen. The goal is not to make the environment look complicated. The goal is to make it predictable and defensible.
4. Implement the required technical controls
At this point, the environment should be small enough and clear enough that control implementation becomes practical.
Focus on the basics that matter most: access control, encryption, secure configuration, vulnerability management, logging, monitoring, and change control. The important thing is not whether the controls sound impressive. It is whether they are consistently applied.
5. Document policies, procedures, and ownership
This is the step that many teams underestimate and later regret underestimating.
Every important control should have an owner. The procedure behind it should be understandable. The review cadence should be clear. The evidence should have a home.
If nobody knows who owns a control, that is usually the first sign the control will be weak in practice.
6. Run a gap assessment
Before formal validation, compare the current state to the PCI requirements and identify what is missing.
A good gap assessment is not only a checklist exercise. It should reveal broader issues too: weak scoping, inconsistent operations, poorly defined ownership, thin documentation, and controls that look stronger on paper than they are in reality.
7. Prepare for assessment and ongoing compliance
This is where the mindset matters.
If the team treats PCI as a finish line, the environment usually starts drifting soon after the first validation cycle. Access expands. Exceptions pile up. New services get added. Documentation goes stale. What looked clean six months ago becomes hard to defend.
A better approach is to treat compliance as part of the operating model. Not a special event. Not a one-time sprint. Just part of how the environment is run.
Common mistakes fintechs should avoid
Some problems show up so consistently that they are worth calling out directly.
One is assuming AWS handles compliance for you. It does not.
Another is allowing PCI scope to spread quietly through shared services, internal tools, and broad access models. That kind of scope growth is easy to miss while the product is moving fast, and painful to unwind later.
A third is buying tools before defining boundaries. Tools can strengthen an already clear environment. They cannot rescue a vague one.
A fourth is delaying documentation until the end. That almost always creates more work than it saves.
And finally, many teams make the mistake of treating PCI like a temporary project. It may begin that way, but it only becomes sustainable when it turns into a repeatable operating practice.
Most PCI trouble does not come from a total lack of security technology. More often, it comes from unclear scope, fuzzy ownership, and rushed preparation.
Final thoughts
PCI compliance on AWS is very achievable for fintechs, but it gets easier when the team stops thinking about it as an audit puzzle and starts treating it as a design and operations problem.
That shift changes the work.
Instead of chasing every control at once, you begin by shrinking the problem. You isolate the systems that matter. You make access harder to misuse. You organize evidence before anyone asks for it. And you keep the operating model clean enough that future growth does not pull half the platform into scope by accident.
That is usually the difference between a manageable PCI effort and a painful one.
If your company is planning a PCI initiative on AWS, start by reviewing the current architecture, the real data flows, and the actual boundaries around payment systems. That first pass often reveals more than any list of tools will.
Want experienced support with PCI-focused AWS security design?
Get professional help with PCI DSS-compliant architecture from scratch or with remediation of your existing system to meet this security standard's requirements. Speak to our AWS-certified experts.
FAQs
Does using AWS make a fintech automatically PCI compliant?
No. AWS provides a strong infrastructure foundation, but your company still has to design, secure, operate, and document its own environment in a way that meets PCI requirements.
What is the first step to becoming PCI compliant on AWS?
The first step is defining scope. You need to know exactly where cardholder data is stored, processed, or transmitted, and which systems can affect that environment.
Why is PCI scope such a big deal?
Because scope determines how much of your environment must be controlled and evidenced. A broader scope means more work, more complexity, and more ongoing overhead.
What usually makes PCI hard for fintechs?
Usually not AWS itself. The main problems tend to be unclear data flows, too many connected systems, weak access control discipline, scattered evidence, and vague ownership.
Is PCI compliance a one-time project?
No. It is ongoing. Environments change, teams change, and controls need to keep working over time.
Should fintechs work with a PCI and AWS partner?
For many companies, yes. A good partner can help reduce scope, improve architecture, strengthen control ownership, and make audit preparation far less chaotic.



