TL;DR:
- Cloud security spending is rapidly increasing, driven by AI threats and complex cloud architectures.
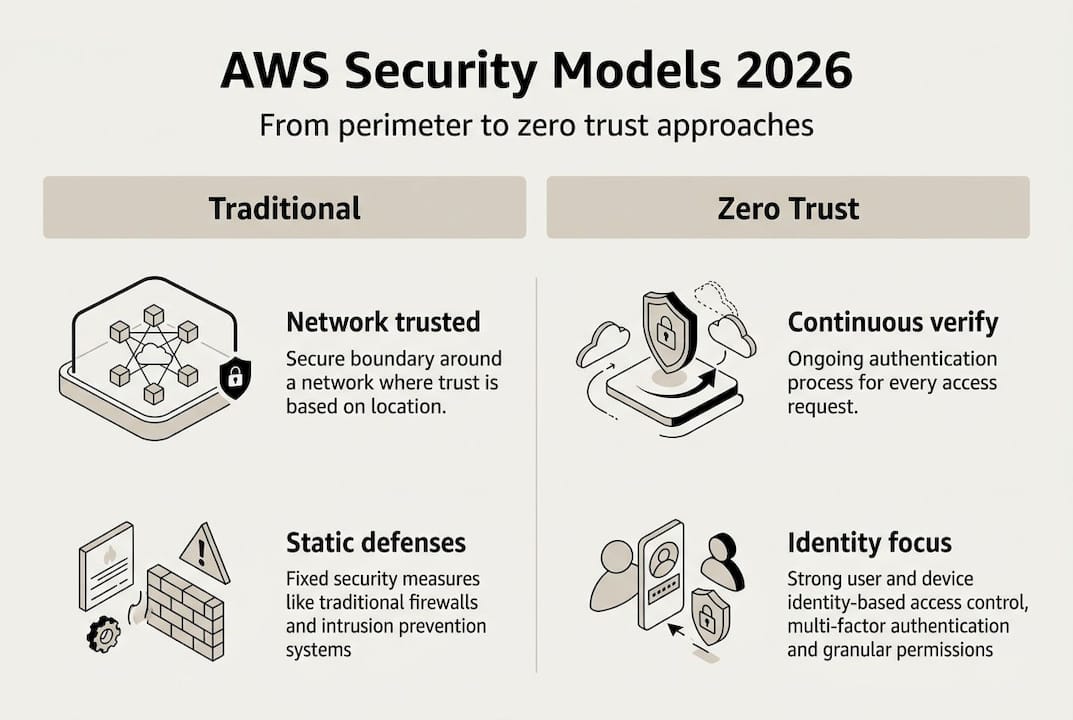
- Zero trust and continuous verification are now essential for AWS security.
- AI and automation enhance threat detection, response, and compliance in AWS environments.
Global security budgets are no longer a line item executives debate — they’re a strategic imperative. With cloud security growing 28.8% faster than any other security segment, the pressure on CIOs and IT leaders managing AWS environments has never been higher. Enterprises and fintech organizations face a converging wave of AI-powered threats, tightening regulations, and increasingly complex cloud architectures. Staying ahead means more than patching vulnerabilities. It means rethinking your entire security posture. This guide breaks down the most critical AWS security trends shaping 2026, the real risks you need to prioritize, and the strategic moves that separate resilient organizations from reactive ones.
Table of Contents
- The 2026 AWS security landscape: Key drivers and risks
- AI and automation: Transforming AWS security operations
- Zero trust and identity: The new perimeter for enterprise AWS
- Compliance and resilience: Building AWS environments for tomorrow’s threats
- Why following trends isn’t enough: The overlooked realities of AWS security
- Strengthen your AWS security posture with IT-Magic
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Cloud security surges | Cloud and AI security investments in 2026 outpace every previous year, raising the bar for AWS defenses. |
| Automation and AI | AI-driven tools and automation dramatically improve AWS security but need careful oversight to avoid risks. |
| Zero trust mentality | Continuous identity verification and zero trust principles replace the old network perimeter mindset. |
| Compliance by design | Regulatory requirements and resilience planning are now core to AWS architecture, not afterthoughts. |
| Culture matters most | Technology changes fast, but organizational awareness and ownership remain the linchpin for true AWS security. |
The 2026 AWS security landscape: Key drivers and risks
The numbers tell a clear story. Cloud security spending is the fastest-growing segment in the entire security market, projected at a 28.8% increase heading into 2026. That growth reflects both the scale of adoption and the scale of the threat. Organizations are moving workloads to AWS at a pace that often outstrips their ability to secure them properly.
Several forces are driving this shift simultaneously. Rapid digital transformation has pushed sensitive workloads — payments, patient data, financial records — into the cloud faster than governance frameworks can keep up. Stricter compliance requirements from regulators across North America, Europe, and Asia-Pacific are raising the bar for what “secure enough” actually means. And AI-powered attacks are no longer theoretical. Threat actors now use machine learning to probe for misconfigurations, automate phishing campaigns, and evade traditional detection tools.
The primary risks you need to watch in 2026 include:
- IAM misconfigurations: Overly permissive roles and policies remain the single most common entry point for attackers in AWS environments.
- Supply chain vulnerabilities: Third-party libraries and software dependencies introduce risk that lives outside your direct control.
- AI-powered attacks: Automated, adaptive attack tools can find and exploit gaps faster than manual security reviews.
- Ecosystem interconnectedness: Multi-cloud and hybrid architectures expand the attack surface in ways that single-environment teams often underestimate.
“Security by design” is no longer a best practice reserved for mature enterprises. Regulators and enterprise customers now expect it as a baseline from any organization running cloud infrastructure.
The good news is that cloud security best practices are maturing rapidly, and AWS continues to expand its native security tooling. But tooling alone won’t close the gap. You need a clear strategy, and the essential security strategies for 2026 look very different from what worked in 2022. The organizations pulling ahead are those treating security as a continuous engineering discipline, not a periodic audit exercise.
AI and automation: Transforming AWS security operations
Artificial intelligence is reshaping what’s possible in cloud security, and AWS is at the center of that shift. AI-amplified security markets could reach $160 billion by 2029, reflecting just how aggressively organizations are investing in AI-driven detection, response, and compliance tools. For AWS environments specifically, this means a new generation of capabilities that can process billions of events per day and flag anomalies in near real time.
Here’s how AI and automation are being applied across AWS security operations today:
- Anomaly detection: Services like Amazon GuardDuty use machine learning to identify unusual API calls, unauthorized access patterns, and suspicious network activity without requiring manual rule-writing.
- Automated remediation: AWS Security Hub integrations can trigger Lambda functions to automatically revoke overly permissive IAM policies or isolate compromised instances the moment a threat is confirmed.
- Compliance reporting: Tools like AWS Config combined with AI-driven analytics can continuously monitor resource configurations and generate audit-ready reports with minimal human effort.
- Threat intelligence enrichment: AI models correlate findings across your environment with global threat feeds, giving your security team context that would take hours to gather manually.
| Capability | Manual approach | AI-automated approach |
|---|---|---|
| Threat detection | Hours to days | Seconds to minutes |
| Incident response | Manual playbooks | Automated remediation |
| Compliance checks | Periodic audits | Continuous monitoring |
| Threat context | Analyst research | Real-time enrichment |
The challenges are real, though. AI models can behave as “black boxes,” making decisions that are difficult to audit or explain to regulators. Bias in training data can cause detection models to miss novel attack patterns. And over-reliance on automation creates a dangerous false sense of security.
Pro Tip: Schedule quarterly reviews where your security team manually examines the decisions made by your AI and ML tools. Automation should accelerate human judgment, not replace it entirely.
Understanding AI in cloud security is increasingly essential for IT leaders. Amazon’s AI advantage in native tooling gives AWS-first organizations a meaningful head start, but only if those tools are configured and monitored correctly.
Zero trust and identity: The new perimeter for enterprise AWS
The old model of perimeter security — a hard shell around a trusted interior — is functionally obsolete in cloud environments. In AWS, there is no physical boundary. Every API call, every service-to-service interaction, and every user session is a potential attack vector. That’s why identity as the security boundary is now the central principle of cloud-native security architecture.
Zero trust means continuous verification. Every request — regardless of where it originates — must be authenticated, authorized, and validated against policy before access is granted. No implicit trust based on network location.
| Dimension | Traditional perimeter | Zero trust model |
|---|---|---|
| Trust assumption | Trusted inside network | No implicit trust anywhere |
| Access control | Broad role-based access | Least privilege, per request |
| Verification | One-time login | Continuous verification |
| Breach impact | Lateral movement risk | Contained blast radius |
IAM misconfigurations are the leading cause of cloud breaches, and AWS environments are no exception. Common mistakes include wildcard permissions in IAM policies, unused service roles with excessive access, and failure to enforce multi-factor authentication on privileged accounts.
Key steps to move toward zero trust on AWS:
- Audit all IAM roles and policies quarterly, removing permissions that are not actively used.
- Enforce MFA across all human users and use IAM roles for service-to-service communication instead of long-lived credentials.
- Implement AWS Organizations with service control policies to enforce guardrails at the account level.
- Use VPC endpoint policies to restrict which services and principals can access resources within your network.
Pro Tip: AWS Identity Center (formerly AWS SSO) gives you centralized access management across multiple accounts. Pair it with attribute-based access control to enforce least privilege dynamically based on user context.
For teams building out their network controls, AWS network security tips provide practical configuration guidance. If you need expert help designing and implementing a zero trust architecture, AWS security consulting can accelerate the process significantly.
Compliance and resilience: Building AWS environments for tomorrow’s threats
Robust identity and access management sets the stage, but compliance and resilience require a broader engineering discipline. Regulations like GDPR, PCI DSS, SOC 2, and emerging regional frameworks in the Middle East and Asia-Pacific are raising the bar for what cloud operators must demonstrate to auditors and customers alike.
As one regulatory body put it, security by design is not just an expectation but increasingly a regulatory requirement. Organizations that treat compliance as a checkbox exercise are the ones that fail audits and breach notifications simultaneously.
Compliance in 2026 is not a point-in-time event. It’s a continuous state that your infrastructure must maintain automatically. The most effective organizations are building compliance into their infrastructure-as-code pipelines, so every resource deployed is checked against policy before it ever reaches production.
Key compliance and resilience practices for AWS in 2026:
- Continuous monitoring: Use AWS Config rules and AWS Security Hub to detect configuration drift the moment it happens, not during the next scheduled audit.
- Automated backup and recovery: Define recovery time objectives and recovery point objectives explicitly, then automate backup schedules and test restoration procedures quarterly.
- Incident response automation: Build runbooks in AWS Systems Manager that automatically execute containment steps when specific GuardDuty findings are triggered.
- Data residency controls: Use AWS Organizations and service control policies to enforce which regions data can be stored in, a critical requirement for GDPR and similar frameworks.
Steps to maintain compliance in a continuously evolving AWS environment:
- Define compliance as code using tools like AWS Config, HashiCorp Sentinel, or Open Policy Agent integrated into your CI/CD pipeline.
- Map every deployed resource to a specific compliance control, so you know exactly what breaks when a configuration changes.
- Run tabletop exercises simulating a breach or compliance failure at least twice per year to validate your incident response playbooks.
- Review AWS compliance strategies regularly as AWS releases new services and compliance frameworks evolve.
Resilience is the other side of this coin. A compliant environment that can’t recover from a ransomware attack or a regional outage is still a liability. Design for failure from day one.
Why following trends isn’t enough: The overlooked realities of AWS security
After more than a decade of delivering 700-plus cloud infrastructure projects, we’ve seen a pattern that no trend report will tell you about. The organizations that suffer the worst security incidents are rarely the ones using outdated technology. They’re the ones with excellent tools and broken processes.
Trend-chasing is genuinely dangerous. Teams adopt zero trust frameworks, deploy AI-powered detection, and invest in compliance automation — then skip the hard work of building organization-wide security mindset across every team that touches the infrastructure. A misconfigured S3 bucket created by a developer who never received security training will bypass every sophisticated control you’ve built.
The uncomfortable truth is that most cloud breaches trace back to human error, unclear ownership, and poor communication between security and engineering teams. Not to technology gaps. Investing in cross-team drills, clear security ownership at the team level, and regular upskilling for engineers will return more security value per dollar than the next tool purchase. The latest AWS security services matter. But they only work when the people operating them understand why each control exists and what to do when an alert fires at 2 a.m.
Strengthen your AWS security posture with IT-Magic
The trends covered in this guide — AI-driven detection, zero trust identity, compliance automation, and resilience engineering — represent real, actionable priorities for 2026. Knowing what to do is one thing. Executing it across a complex AWS environment, while keeping your business running, is another challenge entirely.
At IT-Magic, we’ve been building and securing AWS environments since 2010, with over 700 projects delivered for enterprises and fintech organizations that can’t afford to get security wrong. Whether you need a full AWS infrastructure support engagement or a targeted AWS security consulting assessment to identify your most critical gaps, our certified AWS security and DevOps engineers are ready to help. Reach out to start a conversation about your 2026 security roadmap.
Frequently asked questions
What makes AWS security different in 2026?
In 2026, AWS security centers on AI-powered threat detection, zero trust architecture, and automated compliance driven by rapid cloud adoption and stricter global regulations. The combination of AI-powered attacks and AI-powered defenses makes continuous monitoring and human oversight more critical than ever.
How can enterprises adopt zero trust on AWS?
Zero trust on AWS is built through continuous verification, least privilege IAM policies, MFA enforcement, and service control policies applied across AWS Organizations. Start with an IAM audit to remove unused permissions before layering in more advanced controls.
What are the best practices for AWS compliance in 2026?
Continuous compliance automation using AWS Config and Security Hub, combined with compliance-as-code in CI/CD pipelines, is the foundation of best practice in 2026. Pair that with regular incident response drills and clearly mapped controls to stay audit-ready at all times.
How does AI improve cloud security for AWS environments?
AI enables rapid threat detection, automated remediation, and predictive analytics that block sophisticated attacks before they escalate in AWS environments. With AI-amplified security markets projected to reach $160 billion by 2029, the investment case for AI-driven AWS security tools is already well established.
Recommended
- AWS cloud security: 7 essential strategies for 2026
- AWS Cloud Security: Best Practices, Tools & Complete Guide | IT-Magic
- Cloud cost optimization strategies for CIOs: a practical guide
- How to Improve AWS Reliability: Expert Steps for CTOs