A lot of cloud compliance conversations start in the wrong place. They begin with tools, checklists, or a scramble to answer whatever regulation is getting attention that quarter. And this is how easily compliance work can drift into box-ticking. DORA changes that dynamic. For fintechs running on AWS, it shifts the conversation from being secure enough to the ability to keep critical services running, recover in a controlled way, and prove we’re ready when something breaks.
That is a meaningful change. Not because DORA invents operational resilience for fintech from scratch, but because it makes resilience a formal expectation across the financial sector. Since it began applying in January 2025, DORA has pushed firms to take a harder look at ICT risk, incident handling, resilience testing, and third-party dependencies, all under one umbrella. For teams on AWS, this is not really a legal drafting exercise. It is an architecture exercise, an operations exercise, and a leadership exercise all at once.
So this article is not a legal explainer. It is a practical look at what DORA changes for AWS cloud architecture, where fintech teams usually run into trouble, and what a sensible response looks like when the goal is a more resilient platform rather than a thicker policy binder.
What DORA actually changes for cloud architecture
Before DORA, many fintechs treated resilience as a blend of good intentions and separate workstreams. Security handled controls. Platform engineers handled uptime. Disaster recovery lived in another document. Vendor management owned supplier reviews. Everyone assumed that, taken together, this added up to resilience.
Sometimes it did. Often it did not.
DORA forces those pieces into one picture. Financial entities now need a structured approach to ICT risk management, incident classification and reporting, operational resilience testing, and oversight of ICT third-party providers. That sounds formal, but the cloud impact is very concrete.
An AWS environment now has to do more than run well on an ordinary day. It has to show that it can:
- contain failures,
- recover critical services in a predictable way,
- support investigations,
- produce evidence,
- and make ownership clear.
That last point matters more than it gets credit for. A lot of outages become worse because nobody is fully sure who owns the decision, the runbook, the dependency, or the approval step. DORA puts pressure on that kind of ambiguity.
It also helps to be clear about what DORA does not do. It does not ban cloud. It does not say every fintech must move to a multi-region architecture tomorrow. It does not imply that a cloud provider should carry the whole burden. What it does is raise the standard for how cloud environments are designed, governed, and tested.
That is why the real architectural question is not which AWS service makes us DORA compliant. There is no single answer to that. The better question is whether our cloud architecture supports resilience in a way we can explain, defend, and test.
The DORA requirements AWS architects should care about most
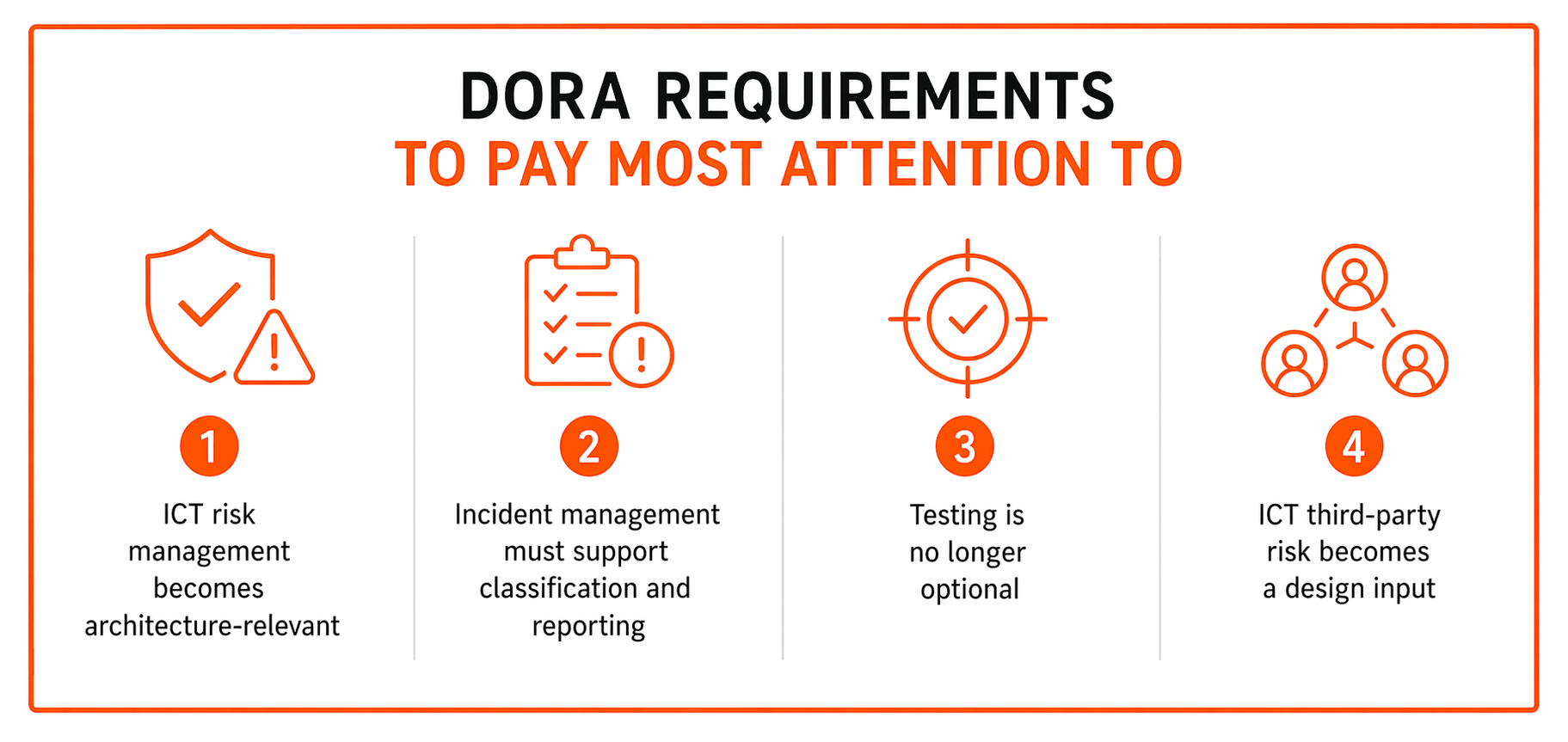
1. ICT risk management becomes architecture-relevant
This is where many leaders feel the shift first. Architecture is no longer just about performance, scalability, and cost. Under DORA, it also becomes part of formal ICT risk management.
In practical terms, that means decisions about network design, identity, logging, backups, change control, workload classification, and dependency mapping are not just technical preferences. They are risk decisions.
Think about a critical customer-facing service such as payment authorization. On paper, that may sound like one application. In reality, it may rely on API gateways, compute services, a database cluster, secrets management, monitoring, IAM roles, alerting, and one or two outside vendors. If any of those pieces fail, the business service is affected. DORA pushes teams to map that chain clearly instead of treating architecture as a collection of disconnected components.
A surprising number of firms still cannot answer a few basic questions quickly:
- Which services are truly critical?
- What supports them?
- Which vendors are in the path?
- What is the accepted recovery target?
- Who signs off on the design?
If those answers live only in people’s heads, the resilience posture is weaker than the leadership team may think.
2. Incident management must support classification and reporting
Resilience is not just about prevention. It is also about seeing trouble early, understanding it fast, escalating it properly, and keeping enough evidence to explain what happened afterward.
That is why logging and monitoring are not just operational nice-to-haves. Under DORA, they become part of the resilience fabric. The EBA’s operational resilience materials make clear that incident handling and reporting are central pieces of the framework.
On AWS, a sound setup should help teams gather:
- a reliable timeline,
- the systems that were affected,
- the changes that happened before the event,
- the dependencies touched by the disruption,
- and the actions taken to restore service.
This is where reality can be messy. Plenty of organizations have “lots of logs” but very little clarity during an incident. Application teams see one part of the picture. Infrastructure teams see another. Security has CloudTrail. A third-party monitoring platform has a different timeline. By the time people piece it together, the pressure is already high.
DORA does not solve that for you, of course. But it does make the weakness harder to ignore.
3. Testing is no longer optional
A recovery plan that has never been tested is not a capability. It is a hypothesis.
That may sound blunt, but it is one of the most important mindset shifts in DORA. The regulation puts weight on fintech operational resilience testing, and for some firms that includes more advanced forms of testing as well.
In AWS environments, that means architecture should support real drills, not ceremonial ones. Good examples include:
- restore tests from backup,
- failover exercises,
- dependency-loss scenarios,
- rollback simulations,
- and break-glass access checks.
The point is not to “pass” a drill. The point is to discover where the design is brittle, where the manual steps still dominate, and where recovery depends on tribal knowledge.
A useful leadership question is about the last recovery test on a critical service, and what failed during that exercise. That question leads to better decisions.
4. ICT third-party risk becomes a design input
Fintechs are rarely dependent on one platform alone. Even when AWS is the core foundation, there are usually other services in the chain: identity providers, payment processors, fraud tools, messaging vendors, monitoring systems, customer support platforms, and more.
DORA puts real emphasis on ICT third-party risk and visibility into these relationships. For architecture teams, that means dependency sprawl has to be treated as a resilience issue, not just a vendor management issue.
AWS also makes it clear that customers still carry major responsibilities under the shared responsibility model. AWS secures the underlying cloud, but customers remain responsible for how they architect workloads, configure access, protect data, and operate services in the cloud.
That is where some fintechs get caught. They assume cloud maturity at the provider level automatically translates into resilience at the workload level. It does not.
_______________________________________________________________________
Get a practical view of where your current setup may be exposed!
Our team can help review cloud design choices, control gaps, and recovery strategy through our AWS security services.
_______________________________________________________________________
What this means in practice for AWS cloud design
Start with business services, not infrastructure diagrams
One of the most useful shifts DORA encourages is this: begin with business services, not the technical estate.
That sounds obvious, yet many architecture reviews still start with a list of AWS components. VPCs. Databases. Kubernetes clusters. Queues. Identity services. All important, yes, but still the wrong first step.
A better starting point is to ask:
- Which customer-facing or regulated services are genuinely critical?
- What supports those services?
- What happens if one region, one vendor, or one internal process goes down?
- Which interruptions would create customer harm, regulatory issues, or reputational damage?
Once that map exists, design choices become easier to defend. Without it, teams often build resilience around the loudest systems rather than the most important ones.
Take customer onboarding as an example. The obvious architecture may be the application stack itself. But the real workflow may also depend on identity verification, messaging, a fraud service, manual review steps, reporting pipelines, and external APIs. If one side dependency breaks the flow, then resilience has to include that side dependency too.
Design around failure domains
Here is where nuance matters.
Resilience improves when teams understand what can fail independently. That might be:
- an Availability Zone,
- an AWS region,
- a third-party service,
- an IAM path,
- a deployment pipeline,
- or even a manual approval process.
AWS guidance makes an important point here. Many availability targets can be achieved within a single AWS region by designing for Multi-AZ fault isolation. Multi-region architectures can be powerful, but AWS does not present them as a default answer for everything. They are better suited to cases with more extreme continuity needs or strong business drivers.
That matters because some firms hear “resilience” and immediately jump to “multi-region everywhere.” In reality, that can create more complexity than value.
A multi-region design may introduce:
- more operational overhead,
- harder data consistency choices,
- more failure paths,
- tougher testing requirements,
- and higher costs.
So DORA should not push fintechs into reflex decisions. It should push them into well-reasoned decisions.
Make recovery design explicit
Recovery is where confidence and reality tend to part ways.
Many teams say they have backups. Fewer can say exactly how long restore takes for a critical workload, who can initiate recovery, what manual steps are still required, or what happens if a dependency needed for recovery is also unavailable.
AWS provides a range of disaster recovery patterns, from simple backup-and-restore approaches to more advanced strategies, along with tools such as AWS Backup and AWS Elastic Disaster Recovery. That is useful, but the hard work still sits with the customer.
A good recovery design should be explicit about:
- recovery time objectives,
- recovery point objectives,
- data replication patterns,
- restore procedures,
- ownership,
- and evidence of testing.
It is worth saying this plainly: redundancy is not the same thing as recoverability. A service may look robust on a diagram and still be difficult to restore under real pressure because the sequence is unclear, access is blocked, or the documentation is stale.
That is exactly the kind of gap DORA tends to expose.
Six architecture areas DORA will likely force fintechs to revisit on AWS
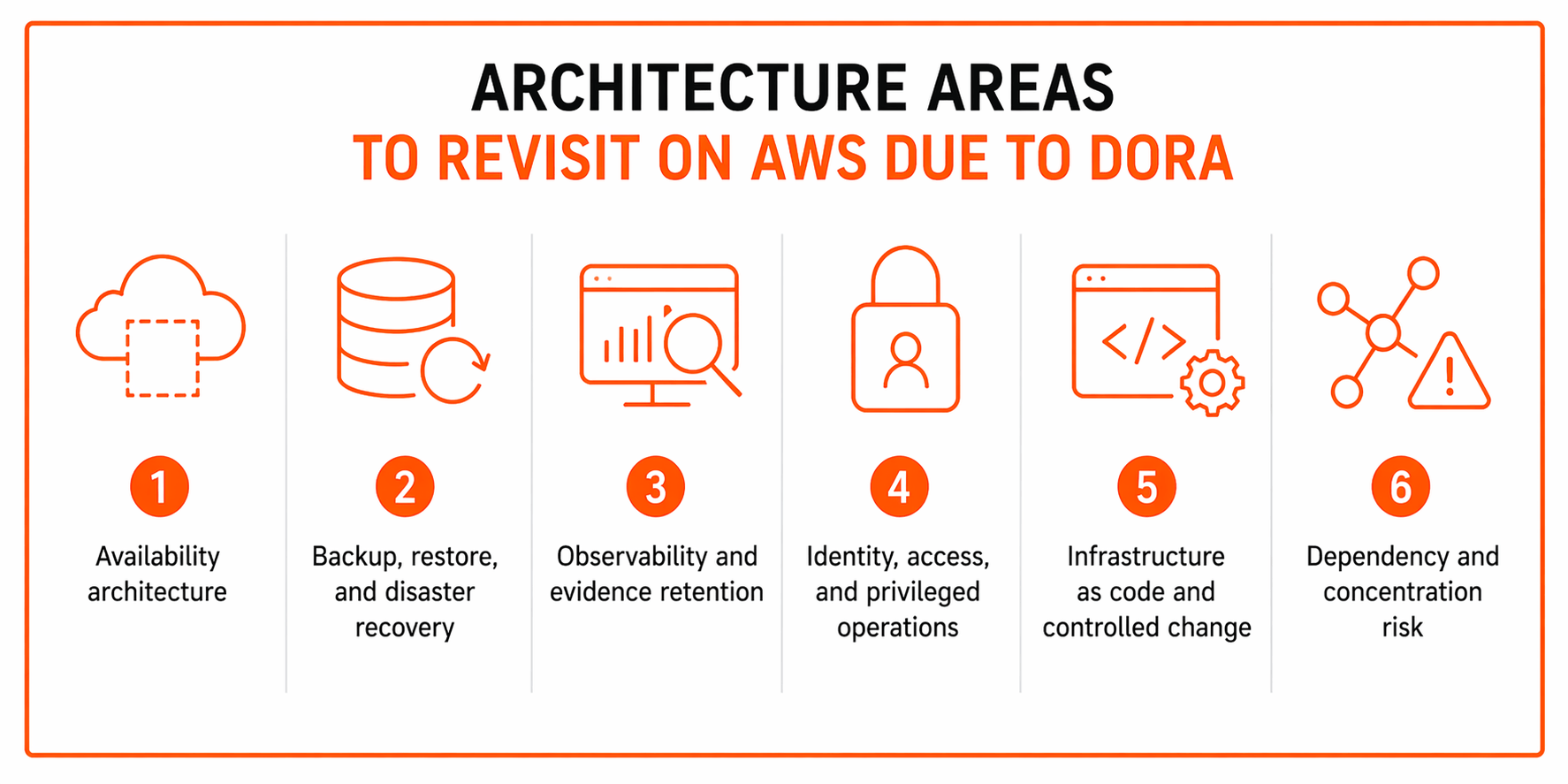
1. Availability architecture
Some workloads are still single-AZ when they should not be. Others are technically Multi-AZ but have hidden single points of failure elsewhere, such as stateful components, brittle integrations, or manual deployment steps.
This is why availability architecture needs a second look. The right pattern depends on business criticality, acceptable downtime, data behavior, and the team’s ability to operate a more complex design safely.
Not every service needs the same architecture. Treating them all the same is usually a mistake.
2. Backup, restore, and disaster recovery
DORA makes tested recovery more important than backup existence alone.
That may sound like a subtle difference, but it is not. Plenty of organizations can point to backup jobs. Far fewer can show regular restore tests, controlled access to backup administration, role separation, retention discipline, and documented restore timing against real service targets.
A restore drill on one representative critical workload is often more revealing than a dozen polished status meetings.
3. Observability and evidence retention
You need telemetry for more than troubleshooting. You need it for incident review, reporting, audit support, and internal accountability.
That means logs and evidence should help answer simple but essential questions:
- who changed what,
- when the change happened,
- which systems were affected,
- what the customer impact was,
- and how recovery unfolded.
If that information is scattered, incomplete, or hard to reconstruct, the operating model still has work to do.
ENISA’s finance sector threat landscape underlines why this matters. Financial organizations continue to face material cyber and operational disruption risks, which makes traceability and evidence retention more than a governance formality.
4. Identity, access, and privileged operations
Operational resilience for fintech is not only about surviving platform failures. It is also about surviving bad access design.
If privileged access is too broad, the risk grows. If emergency access is too narrow or untested, recovery may stall. If only one team can perform a critical action and that team is unavailable, the architecture is not as resilient as it looks.
That is why least privilege, MFA, role separation, hardened administrative paths, and tested emergency access deserve a place in any serious DORA response.
5. Infrastructure as code and controlled change
When environments are defined in code, reviewed in pipelines, and tracked in version control, both auditability and recovery improve. That does not solve every problem, but it reduces uncertainty.
Manual console changes, undocumented exceptions, and tribal fixes create the opposite effect. They may feel quick in the moment, yet they make systems harder to understand and harder to recover later.
This is one place where engineering discipline quietly becomes a resilience advantage.
6. Dependency and concentration risk
A fintech may be comfortable with AWS itself and still have significant exposure elsewhere.
Identity platforms, payment vendors, monitoring providers, messaging systems, and fraud tools can all become concentration risks if too much depends on one provider without a credible fallback.
A practical question helps here: if this external dependency failed for a day, what critical service would stop, and what would we do next?
That question is not theoretical. It often reveals that the real weak point sits outside the main AWS estate.
The shared responsibility trap: where fintechs still own the hard parts
This is the part that is easiest to misunderstand.
AWS offers resilient infrastructure, a large compliance program, DORA-related guidance, and access to reports through AWS Artifact. But those things support your resilience posture. They do not replace it.
Customers still own a large share of the hard work, including:
- workload design,
- access models,
- backup policy,
- incident process,
- supplier dependency oversight,
- and evidence of control operation.
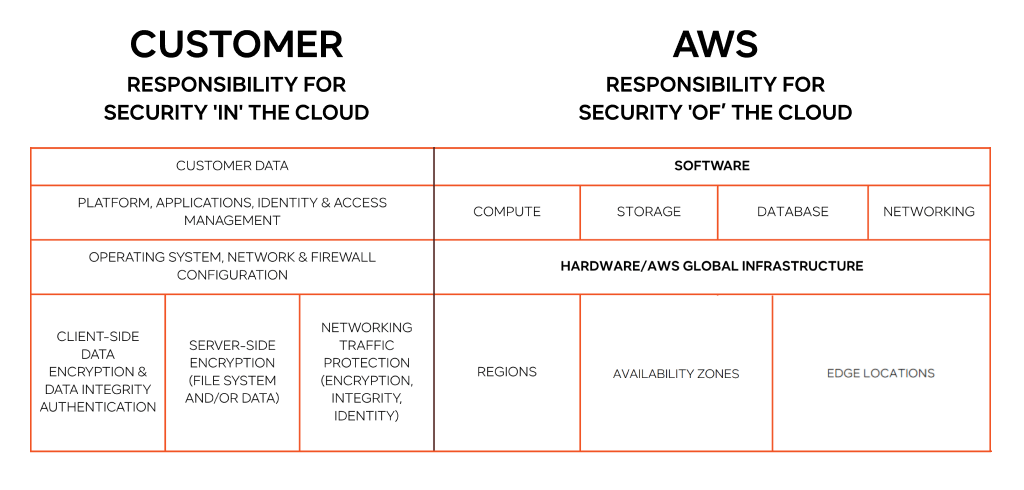
That is why it is risky to assume cloud maturity equals workload maturity. It does not. A strong provider can still host a weak operating model.
The simple truth is this: cloud compliance support is not the same thing as compliance by default.
A practical response plan for fintech teams on AWS
Step 1. Identify critical services and map dependencies
Start with the business services the regulator, the customer, and the executive team would care about most if they failed.
Map the systems, data paths, vendors, people dependencies, and runbooks behind each one. Include the messy side paths too. Support tooling, exports, reporting, and manual approvals often matter more during disruption than teams expect.
Step 2. Assess current resilience posture
Compare the environment on paper with the environment in practice.
Look at:
- failure domains,
- access paths,
- backup design,
- observability coverage,
- deployment risk,
- and dependency concentration.
Then ask what is actually tested rather than what is merely documented.
Step 3. Prioritize the biggest architecture gaps
Not every issue belongs in the first wave. Focus first on the weaknesses that create the biggest business and regulatory exposure.
Typical examples include unclear failover paths, untested restores, poor evidence retention, overreliance on one vendor, and blurred ownership boundaries.
Step 4. Build evidence into operations
Do not wait for an audit to gather proof. Build it into routine work.
That includes change records, recovery test results, incident timelines, architecture decisions, access reviews, and control checks. AWS Artifact is useful because it gives customers access to AWS compliance reports and related documents, but internal evidence is what shows how your environment really operates.
Step 5. Test, learn, refine
Run realistic exercises. Restore data. Simulate dependency loss. Review outcomes. Improve the design. Repeat.
That cycle matters because resilience is never finished. It gets better through repetition, honesty, and pressure-testing.
Conclusion
DORA does not ask fintechs to produce prettier documents around fragile systems. It asks them to operate critical services in a way that can stand up to disruption and scrutiny.
For AWS environments, the biggest change is not one service choice or one design pattern. It is the move toward architecture that is explainable, testable, observable, and tied to clear ownership.
The firms that take that seriously will not just be better prepared for regulatory review. They will probably run steadier platforms, make cleaner decisions, and recover faster when the inevitable disruption comes.
The best DORA response is not more paper. It is better architecture, tested regularly, with evidence built into everyday operations.
Turn DORA from a vague compliance concern into a practical AWS roadmap!
Contact IT-Magic for cloud consulting, resilience planning, and AWS security services that support a stronger operational foundation.
FAQs
Does DORA require fintechs on AWS to use multi-region architecture?
No. AWS guidance supports strong single-region resilience with Multi-AZ design for many workloads. Multi-region becomes more relevant when business impact, continuity targets, or other drivers justify the extra complexity. The important part is to justify the choice and test it.
Is using AWS enough to satisfy DORA?
No. AWS provides infrastructure, guidance, and compliance resources, but customers still own many core resilience decisions and operational controls under the shared responsibility model.
What parts of DORA matter most for cloud architecture?
The most relevant areas are ICT risk management, incident handling and reporting, resilience testing, and ICT third-party risk management. Those are the parts that most directly influence architecture and operations.
Does DORA focus only on cybersecurity?
No. Cybersecurity is part of the picture, but DORA is broader than that. It is about whether financial entities can withstand, respond to, and recover from ICT disruptions, including operational failures and third-party issues.
What is the biggest mistake fintechs make when preparing for DORA on AWS?
Treating it as a documentation exercise instead of an architecture and operating model exercise. Policies help, but they do not compensate for weak recovery paths, poor visibility, and untested controls.
How can AWS help with DORA readiness?
AWS can help with DORA-related guidance, reliability best practices, disaster recovery options, the shared responsibility framework, and access to compliance materials through AWS Artifact. Those resources are helpful, but they work best when paired with a clear internal resilience plan.




