TL;DR:
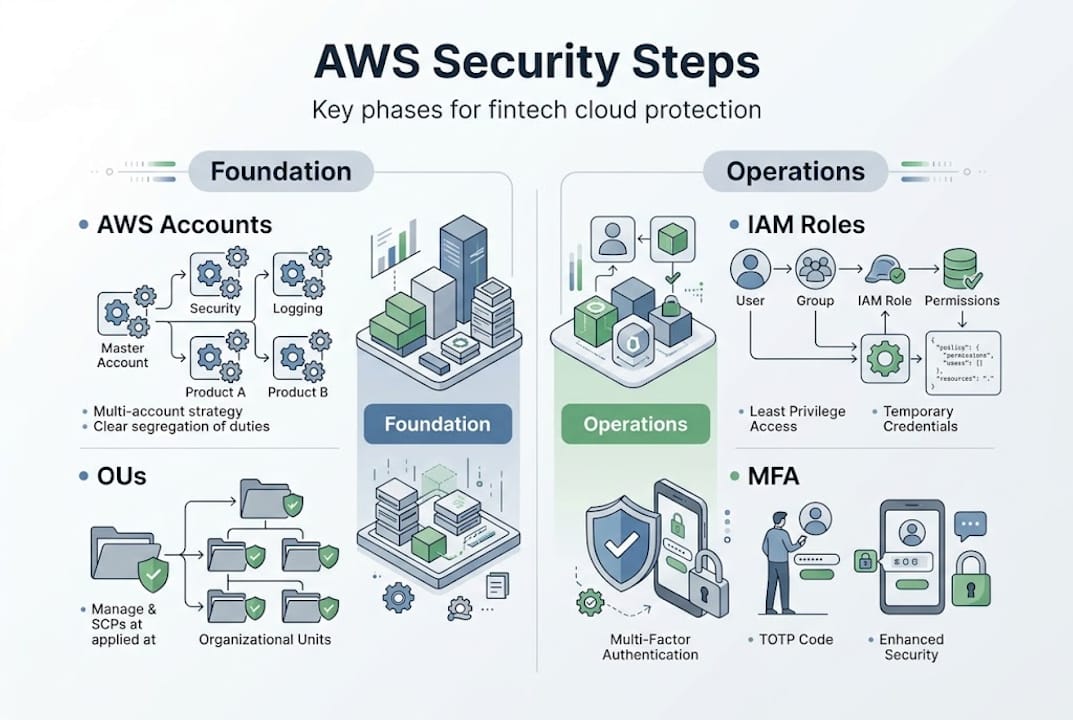
- Structuring AWS accounts with organizational units and SCPs is essential for workload isolation and regulatory compliance.
- Implementing least privilege access, MFA, and continuous permission reviews strengthen identity security.
- Continuous monitoring, layered defenses, and automated incident response are vital for detecting and mitigating threats.
A single cloud misconfiguration in a fintech environment can expose millions of customer records, trigger regulatory penalties, and permanently damage trust. The stakes are not abstract. AWS provides powerful native controls, but knowing which to activate, in what order, and how to automate them is what separates resilient financial platforms from vulnerable ones. This guide walks engineering leaders through expert-vetted architecture steps grounded in the AWS Security Reference Architecture, covering organizational isolation, identity management, continuous monitoring, layered defenses, and automated incident response.
Table of Contents
- Establishing a secure AWS foundation: Organizational units and account structure
- Building a robust identity foundation: IAM, least privilege, and MFA
- Continuous detection and traceability: Monitoring, logging, and automation
- Implementing defense in depth: Layered infrastructure and data protection
- Automating incident response and preparing for security events
- Why fintech leaders need a stepwise, automation-first approach
- Partner with AWS experts to secure your fintech cloud
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Start with AWS Organizations | Isolating workloads and enforcing governance at the root is critical for secure fintech environments. |
| Enforce strong identity management | Implement least privilege, enable MFA, and regularly audit IAM permissions to reduce risk. |
| Automate detection and response | Centralized logging, threat modeling, and incident response automation protect compliance and uptime. |
| Layer defenses across all levels | Combine network, compute, and encryption controls for true defense in depth. |
| Quarterly review and adapt | Threats and requirements change—review architecture and controls regularly for continued security. |
Establishing a secure AWS foundation: Organizational units and account structure
Every reliable fintech cloud deployment starts with the same question: how do you prevent one compromised workload from affecting everything else? The answer is structural separation, not just configuration.
The Well-Architected Security Pillar defines the first core step clearly: build your OU and account structure using AWS Organizations for workload isolation. This is not optional for regulated environments. It is the foundation that every other control depends on.
Start by mapping your business to organizational units (OUs). Common groupings for fintech include:
- Production workloads with strict access controls and change management
- Non-production environments (dev, staging, QA) with relaxed but still audited policies
- Security and logging accounts that are write-protected from all other OUs
- Shared services for centralized tooling like CI/CD pipelines or DNS
- Sandbox accounts for experimentation, isolated from all regulated data
This structure limits blast radius. If an attacker compromises a developer sandbox, they cannot pivot to production because the account boundary itself is a hard wall. This is fundamentally different from relying on security groups or IAM alone, which can be misconfigured.
The AWS Security Reference Architecture (SRA) formalizes this as a landing zone. A landing zone is a pre-configured, multi-account AWS environment that enforces governance from day one. It includes centralized logging, guardrails via Service Control Policies (SCPs), and a dedicated security account. For fintech teams, this baseline is what auditors expect to see when reviewing PCI DSS or SOC 2 compliance posture.
| Attribute | Flat account structure | Multi-account structure |
|---|---|---|
| Blast radius | High: one breach affects all | Low: isolated per workload |
| Regulatory alignment | Difficult to demonstrate | Clear audit boundaries |
| Permission management | Complex and error-prone | Scoped per account |
| Cost visibility | Blended and unclear | Per-workload attribution |
| Scalability | Degrades with team size | Scales with governance intact |
You can also review network security tips for complementary controls that work alongside this account structure. If you are evaluating how AWS compares to other providers on security posture, the AWS competitors for security analysis is worth reading before committing to a multi-cloud strategy.
Pro Tip: Apply Service Control Policies at the OU level before you onboard any workloads. SCPs act as a permission ceiling, meaning even account administrators cannot exceed what the SCP allows. This prevents privilege escalation at the organizational level and is far harder to bypass than account-level IAM policies.
Building a robust identity foundation: IAM, least privilege, and MFA
With your baseline isolated accounts, the next pillar is managing exactly who can do what inside your environment. Identity is the most exploited attack surface in cloud environments, and fintech platforms are a high-value target.
The Well-Architected Security Pillar is direct: implement a strong identity foundation with IAM Identity Center, least privilege, and MFA. Here is how to execute that in practice.
- Deploy IAM Identity Center as your single sign-on entry point across all accounts. Federate it with your existing identity provider (Okta, Azure AD, or Google Workspace) so that user lifecycle management happens in one place.
- Define permission sets that reflect actual job functions, not convenience. A developer should not have production write access. An auditor should have read-only access to logs, nothing more.
- Enable MFA for every human identity. For privileged roles, require hardware MFA tokens or passkeys, not just TOTP apps.
- Audit existing permissions using IAM Access Analyzer to identify unused roles, overly broad policies, and cross-account access that was never formally reviewed.
- Use the AWS Well-Architected Tool to run periodic AWS identity strategies reviews against your IAM configuration and flag high-risk items.
Here is a practical reference for role scoping in a fintech environment:
| Role | Allowed actions | Denied by SCP |
|---|---|---|
| Developer (non-prod) | Deploy to dev/staging, read logs | Production write, IAM changes |
| Security auditor | Read all logs, view Config rules | Any write or delete action |
| Platform admin | Manage infra, update SCPs | Direct data access, billing changes |
| CI/CD pipeline | Deploy to production via approved pipeline | Console access, IAM modification |
Notice that the CI/CD pipeline role has no console access. That is intentional. Automation should never need a human-facing interface, and restricting it reduces the attack surface significantly.
For cloud consulting insights on structuring teams around these access models, the broader pattern of separating deployment authority from data access is a recurring theme in regulated industries.
Pro Tip: Never use long-lived access keys for programmatic access. Use IAM roles with temporary credentials via AWS STS instead. Long-lived keys are a liability: they get committed to repositories, shared in Slack, and forgotten in CI/CD configurations for years.
Continuous detection and traceability: Monitoring, logging, and automation
Once strict identity controls are in place, visibility into actions and changes is key to prevent and respond to incidents. You cannot defend what you cannot see.
The Well-Architected Security Pillar requires maintaining traceability with CloudTrail, Config, and centralized logging. For fintech, this is also a compliance requirement under PCI DSS requirement 10, which mandates audit trails for all access to cardholder data environments.
Set up CloudTrail across all accounts and regions, writing to a centralized S3 bucket in your security account. Enable log file validation so you can prove logs have not been tampered with. AWS Config should run continuously, recording every resource change and evaluating it against managed or custom rules.
What to capture and where to review it:
- CloudTrail management events: All API calls, including read-only, for privileged accounts
- CloudTrail data events: S3 object-level access and Lambda invocations in production
- VPC Flow Logs: Network traffic patterns for anomaly detection
- Config snapshots: Point-in-time resource configurations for forensic review
- Security Hub findings: Aggregated across GuardDuty, Inspector, Macie, and Config
“Continuous monitoring and automation at scale are essential for maintaining a strong security posture as your environment grows and evolves.” — AWS Security Reference Architecture
Security Hub is particularly valuable because it benchmarks compliance against standards like CIS AWS Foundations and PCI DSS automatically. Review your Security Hub score weekly, and schedule formal threat modeling sessions at least quarterly per SEC01-BP07 guidance. The Well-Architected Security Pillar recommends using Security Hub scores and the Well-Architected Tool together to identify high-risk and medium-risk items before they become incidents.
For payment-specific controls, payment security best practices offer additional context on what regulators and card networks expect from your monitoring posture.
Implementing defense in depth: Layered infrastructure and data protection
With detection in place, actual mitigation relies on layered defenses and airtight data security. Defense in depth means no single control failure exposes your entire environment.
The Well-Architected Security Pillar is explicit: apply security at all layers, including network segmentation via VPC layers, security groups, and NACLs, compute protection through Inspector, and WAF for applications. Protect data in transit and at rest with KMS encryption and TLS.
Here is how to layer these controls in practice:
- Network perimeter: Deploy AWS WAF in front of all public-facing APIs and web applications. Configure managed rule groups for OWASP Top 10 threats and add custom rules for your specific traffic patterns.
- VPC segmentation: Separate subnets for public-facing load balancers, application tiers, and databases. Use security groups as stateful firewalls scoped to the minimum required ports and source ranges. Add NACLs as a stateless secondary layer for explicit deny rules.
- Compute hardening: Run AWS Inspector continuously against EC2 instances and container images. Inspector identifies unpatched CVEs and network exposure automatically, generating prioritized findings you can feed into your remediation pipeline.
- Data at rest: Encrypt all S3 buckets, RDS instances, EBS volumes, and DynamoDB tables using AWS KMS customer-managed keys. This gives you full control over key rotation and access auditing.
- Data in transit: Enforce TLS 1.2 or higher on all endpoints. Use ACM to manage certificates and set up automated renewal so expired certificates never become an outage or a vulnerability.
You can find detailed VPC security best practices for subnet design and security group rule management. For teams scaling these controls across dozens of accounts, scalable AWS security patterns address how to manage this consistently through infrastructure as code.
Pro Tip: Rotate KMS keys annually at minimum, and validate key policies quarterly. Overly permissive key policies, especially those granting kms:* to broad principals, are a common audit finding that can put your PCI DSS certification at risk. Also review data protection practices for additional context on securing sensitive information at the device and application layer.
Automating incident response and preparing for security events
Even robust detection and prevention cannot stop every possible threat. Rapid, reliable response is your last line of defense, and in fintech, regulators expect you to demonstrate it.
The Well-Architected Security Pillar is clear: prepare for security events with GuardDuty and incident response automation. For PCI DSS compliance, you need documented response procedures and evidence that they actually work.
GuardDuty is your continuous threat detection engine. It analyzes CloudTrail logs, VPC Flow Logs, and DNS queries using machine learning to surface anomalies like unusual API call patterns, cryptocurrency mining activity, or communication with known malicious IPs.
Common triggers worth automating responses for:
- Malicious API calls from unusual geographic locations
- IAM credential exfiltration attempts
- Network traffic to known command-and-control infrastructure
- Unusual S3 data access volumes (potential exfiltration)
- Root account usage outside of approved maintenance windows
Here is a practical runbook structure for your incident response program:
- Define playbooks as code using AWS Step Functions or Lambda. Each GuardDuty finding type should map to a specific automated response, such as isolating an EC2 instance, revoking IAM credentials, or blocking an IP in WAF.
- Establish severity tiers with clear escalation paths. A low-severity finding might create a ticket automatically. A high-severity finding should page your on-call team within two minutes.
- Run tabletop exercises quarterly. Walk your team through a simulated breach scenario without touching production. Document gaps and update playbooks accordingly.
- Test automated responses in a non-production account monthly. Automation that has not been tested is automation you cannot trust during an actual incident.
For incident response planning that aligns with compliance requirements, the key insight from AWS SRA is to treat incident response as code. Version-controlled, tested, and deployed like any other infrastructure component.
Why fintech leaders need a stepwise, automation-first approach
Here is an uncomfortable truth: most fintech security failures are not caused by missing tools. They are caused by the order in which controls were added.
Teams build fast, ship product, and layer security on afterward. The result is a patchwork of controls with gaps between them, manual processes that fail under pressure, and audit findings that require emergency remediation. We have seen this pattern repeatedly across financial services clients.
The stepwise approach in this guide is not just logical. It is strategic. When you automate detection before you have an incident, you build institutional knowledge into your systems rather than your people. When you define cloud security strategies at the account structure level, every workload you add inherits those controls automatically.
The fintechs that treat their landing zone, IAM model, and incident response playbooks as living infrastructure, reviewed and upgraded quarterly, are the ones that pass audits without emergency sprints. That discipline is a competitive advantage, not just a compliance checkbox.
Partner with AWS experts to secure your fintech cloud
If you’d rather not leave security to chance, leverage specialized expertise to accelerate your roadmap.
At IT-Magic, we have spent over a decade designing secure, compliant AWS environments for fintech and enterprise clients. Our AWS for fintech practice covers everything in this guide, implemented as production-grade infrastructure from day one. We also provide Kubernetes support for secure fintech environments, including EKS hardening and container image scanning pipelines. In our Foxtrot migration case study, we delivered a secure cloud migration with measurable cost reduction and zero compliance gaps. If you want certified AWS specialists to review your current architecture and identify the highest-priority risks, reach out to schedule a security assessment.
Frequently asked questions
What is the first step to ensure secure AWS cloud architecture for fintech?
The initial step is creating a solid organizational unit and account structure using AWS Organizations to isolate workloads and apply governance, as recommended by the Well-Architected Security Pillar. This structural separation limits blast radius and establishes the foundation for all subsequent controls.
How often should I review access permissions in a fintech AWS environment?
Review IAM roles and permissions quarterly or after any significant team or regulatory change. The Well-Architected Security Pillar recommends using the AWS Well-Architected Tool for periodic IAM reviews to catch drift before it becomes a compliance finding.
Which AWS services help automate incident response?
GuardDuty provides continuous threat detection, and automation can be implemented with Lambda or Step Functions to trigger incident playbooks automatically. The Well-Architected Security Pillar recommends treating these playbooks as code, versioned and tested like any other infrastructure component.
Why is defense in depth important for fintech cloud architectures?
Defense in depth uses layers of independent controls so that no single misconfiguration or breach exposes your entire environment. The Well-Architected Security Pillar specifies applying security at every layer, from network segmentation with VPC, security groups, and NACLs to compute protection with Inspector and WAF, making it the standard for regulated financial workloads.
Recommended
- AWS for Fintech | PCI DSS-Ready, Secure & Scalable Infrastructure
- 5 key benefits of AWS infrastructure for fintech
- How Managed IT Services Transform AWS for Fintech
- PCI DSS on AWS: A Clear Path to Audit Readiness | IT-Magic