TL;DR:
- Effective AWS governance requires deliberate policies, controls, and processes to manage access, compliance, and costs.
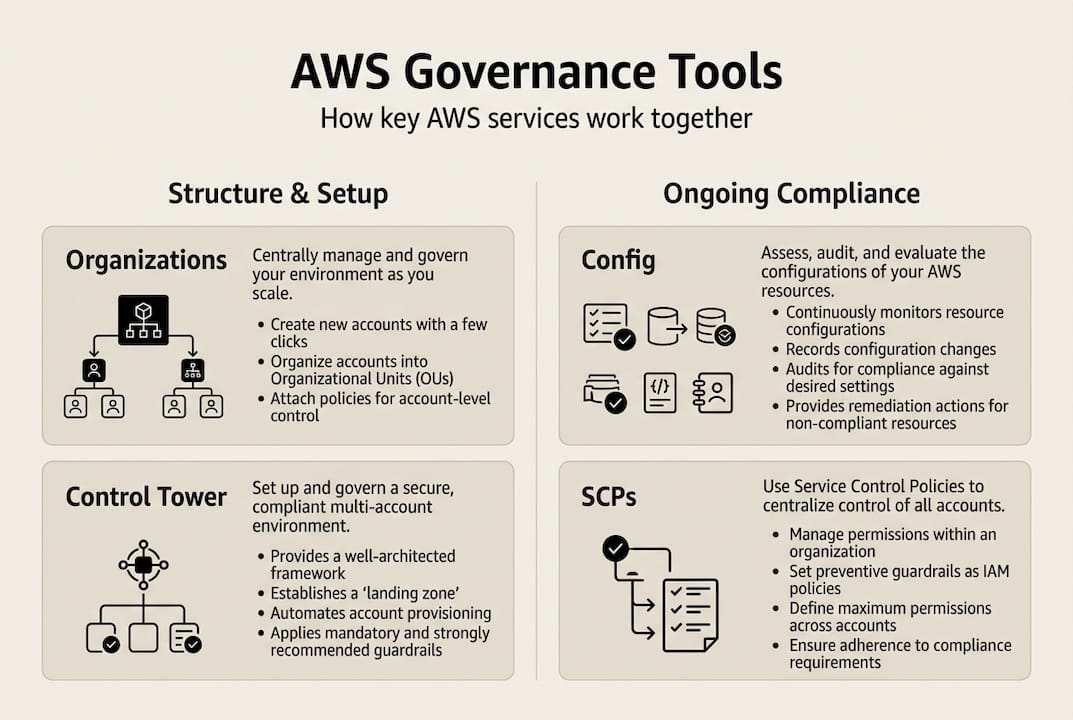
- Key services include AWS Organizations, Control Tower, Config, and Audit Manager, which work together to enforce policies and ensure compliance.
- Building a scalable governance framework accelerates innovation, reduces risks, and simplifies audits across startups, fintech, and enterprises.
Many IT leaders assume that migrating to AWS automatically brings security, compliance, and cost control. It does not. Without a deliberate governance structure, you get sprawling accounts, unpredictable bills, and audit failures at the worst possible time. AWS governance is the framework that prevents those outcomes, and getting it right is one of the highest-leverage investments a cloud team can make. This guide breaks down what AWS governance actually means, which services power it, how to implement it, and what traps to avoid, whether you are running a fast-growing startup, a regulated fintech, or a large enterprise.
Key Takeaways
| Point | Details |
|---|---|
| Governance is essential | Without governance, AWS environments quickly become risky and costly. |
| Use AWS native tools | AWS Organizations, Control Tower, and Config together provide comprehensive governance controls. |
| Tailor strategy by business type | Startups, fintech, and enterprises each need different governance approaches for compliance and scalability. |
| Test before production | Sandbox and stage SCPs and guardrails before enforcing them in production environments. |
Understanding AWS governance: Definition, scope, and why it matters
AWS governance is not a single feature you turn on. It is a coordinated set of policies, controls, and processes that define how your organization uses AWS. At its core, AWS governance involves managing access, compliance, and resource usage within cloud environments. That covers everything from who can spin up an EC2 instance to how your audit logs are stored and reviewed.
Without governance, three problems surface fast:
- Shadow IT: Teams provision resources outside approved channels, creating untracked spend and unpatched infrastructure.
- Security gaps: Overly permissive IAM roles and public S3 buckets become liabilities that auditors and attackers both find.
- Cost overruns: Unused resources, untagged workloads, and right-sizing failures quietly drain budgets.
With governance in place, the picture changes. Compliance audits that used to take weeks can be completed in days because evidence is already collected and organized. Teams move faster because guardrails replace manual approval bottlenecks. Scaling does not introduce new risk because policies travel with the infrastructure.
Governance is not about slowing teams down. It is about making sure speed does not come at the cost of security or compliance.
For fintech companies, this is not optional. PCI DSS, SOX, and other regulatory frameworks require demonstrable controls over who accesses cardholder data, how changes are tracked, and how incidents are reported. Health tech and other highly regulated industries face similar mandates. Even startups that are not yet regulated benefit from building governance early, because retrofitting controls onto a chaotic environment is far more expensive than starting clean.
Good AWS cloud security best practices always start with governance as the foundation. Security tools are only as effective as the policies and account structures supporting them.
Key AWS services for governance: How the tools fit together
AWS Organizations, Control Tower, and Config all play unique roles in governance, and understanding how they connect is essential before you start building.
| Service | Primary function | Key governance role |
|---|---|---|
| AWS Organizations | Multi-account management | Apply Service Control Policies (SCPs) across accounts |
| AWS Control Tower | Automated landing zones | Deploy guardrails, enforce baseline security |
| AWS Config | Resource configuration monitoring | Detect drift, audit changes, trigger alerts |
| AWS Audit Manager | Compliance evidence collection | Automate reporting for PCI DSS, SOX, HIPAA |
Here is how they work together in practice:
- AWS Organizations is the structural backbone. It groups accounts into Organizational Units (OUs) and applies SCPs that define what actions are allowed or denied across those accounts.
- AWS Control Tower sits on top of Organizations and automates the setup of a secure, multi-account environment called a landing zone. It comes with pre-built guardrails, both preventive (blocking risky actions) and detective (alerting when something drifts).
- AWS Config continuously records resource configurations and evaluates them against rules you define. If a security group opens port 22 to the world, Config catches it.
- AWS Audit Manager pulls evidence from Config, CloudTrail, and other sources to build audit-ready reports aligned to specific compliance frameworks.
A useful way to think about it: Organizations defines the structure, Control Tower enforces the baseline, Config watches for drift, and Audit Manager proves compliance. Each layer depends on the others.
For industries like retail, the governance model also needs to account for seasonal traffic spikes and multi-region complexity. Seeing how AWS governance in retail is applied shows how these tools scale across different operational contexts.
One statistic worth noting: organizations using automated compliance tools reduce audit preparation time by up to 60% compared to manual processes. That is not a minor efficiency gain. It is the difference between a compliance team that is always firefighting and one that is actually improving controls.
Implementing AWS governance: Core strategies and best practices
Knowing the tools is one thing. Putting them together in a way that actually works takes deliberate design. Here is a practical sequence:
- Start with a multi-account structure. A single AWS account for everything is a governance anti-pattern. Use Organizations to create separate accounts for production, staging, development, and security tooling. Each account is an isolation boundary.
- Define your OU hierarchy. Group accounts by business unit, environment, or compliance requirement. SCPs applied at the OU level cascade down to all accounts within it.
- Deploy Control Tower for your baseline. Start with Control Tower for baseline guardrails, then refine policies with Organizations and SCPs as your needs grow.
- Choose your SCP approach. Allow-list SCPs only permit explicitly listed actions, making them highly secure but operationally rigid. Deny-list SCPs block specific high-risk actions while allowing everything else, offering more flexibility for teams that need to move fast.
- Test before you deploy broadly. Test SCPs in sandbox OUs before production to avoid breaking live workloads with an overly restrictive policy.
Comparison: Allow-list vs. deny-list SCPs
| Approach | Security level | Operational flexibility | Best for |
|---|---|---|---|
| Allow-list | Very high | Low | Regulated environments, fintech |
| Deny-list | High | High | Startups, fast-moving teams |
Pro Tip: Before rolling out any SCP to a production OU, run it in a sandbox account with a replica of your workload for at least one full sprint cycle. Unexpected permission errors in production are costly and stressful to debug under pressure.
A Well-Architected governance review is a structured way to assess whether your current setup aligns with AWS best practices and identify gaps before they become incidents.
Nuances, pitfalls, and evolving trends in AWS governance
Most governance failures are not caused by choosing the wrong tool. They are caused by misunderstanding the trade-offs between tools and skipping the unglamorous work of testing and iteration.
The biggest architectural decision is whether to use Control Tower or build your own structure manually with Organizations. Control Tower is prescriptive, while manual Organizations allows fine-grained tuning. Control Tower gets you to a secure baseline faster, but it makes assumptions about your account structure and landing zone design. If your environment is complex or you have existing accounts with legacy configurations, those assumptions can create friction.
Common pitfalls to watch for:
- Skipping policy testing: Deploying SCPs directly to production OUs without sandbox validation is one of the most common causes of outages during governance rollouts.
- Over-complicating policies: A governance framework with hundreds of custom rules that no one understands is worse than a simple one that is actually followed.
- Ignoring tagging from day one: Native AWS tools have limited visibility into untagged resources. Without consistent tagging, cost allocation and security reporting become guesswork.
- Neglecting baseline reviews: Governance is not a one-time project. Policies need to evolve as your workloads and compliance requirements change.
The most dangerous governance gap is the one you do not know exists. Regular reviews are not bureaucracy. They are how you find out what has drifted.
On the topic of third-party tools: they can fill real gaps in tagging, observability, and multi-cloud reporting. But they add cost and complexity. Start with native AWS services and add third-party tools only when you have a specific, measurable gap they address.
Understanding cloud migration best practices is also relevant here, because governance decisions made during migration set the tone for everything that follows.
Real-world applications: Case scenarios for startups, fintech, and enterprises
Governance looks different depending on where you are in your growth journey. The AWS Cloud Operating Model applies to both startups and enterprises, but the priorities shift significantly.
Startups are optimizing for speed and flexibility without creating technical debt they will regret later. The right approach:
- Deploy Control Tower early to get guardrails without heavy manual configuration.
- Use deny-list SCPs to allow experimentation while blocking the highest-risk actions.
- Enforce tagging from the start so cost visibility scales with the team.
- Keep the account structure simple but designed to grow, with separate dev and prod OUs.
Fintech companies operate under strict regulatory requirements. PCI DSS, SOX, and sometimes GDPR all demand demonstrable controls. The focus shifts to:
- Layered access control using SCPs plus IAM permission boundaries.
- Immutable audit logs with CloudTrail and Config enabled in every account.
- Audit Manager configured for PCI DSS or SOX frameworks to automate evidence collection.
- Strict network segmentation and encryption controls enforced through preventive guardrails.
Large enterprises often have hybrid environments, legacy systems, and dozens of teams with different requirements. Their governance model needs:
- Custom OU hierarchies that map to business units and regulatory domains.
- Fine-grained SCPs that balance central control with team autonomy.
- Integrated reporting pipelines that pull from multiple accounts into a single compliance dashboard.
- Regular Well-Architected reviews to catch drift across a large, distributed environment.
Working with top AWS partners who have experience across these scenarios can significantly reduce the time it takes to get governance right.
Our perspective: Beyond compliance—Why governance is your cloud growth engine
Most organizations treat governance as a cost center, something they do to satisfy auditors or check a compliance box. That framing is wrong, and it leads to governance programs that are minimal, reactive, and resented by engineering teams.
Here is what we have seen across 700+ projects: the companies that invest in governance early move faster, not slower. When your account structure is clean, your policies are tested, and your guardrails are in place, engineers stop asking for permission and start shipping. The governance framework becomes the answer to “is this safe to do?” instead of a blocker.
The uncomfortable truth is that most cloud incidents, whether a data breach, a runaway bill, or a failed audit, trace back to a governance gap that existed for months before anyone noticed. Strong governance does not prevent innovation. It prevents the kind of incident that stops innovation cold.
Exploring cloud strategy insights can help you frame governance as a business enabler rather than an IT overhead.
Accelerate your AWS governance journey with expert support
Building AWS governance from scratch is complex, and the cost of getting it wrong is high. Whether you are starting fresh or auditing an existing environment, having the right expertise makes the difference between a governance framework that works and one that creates more problems than it solves.
At IT-Magic, we design, build, and audit secure AWS environments for startups, fintech, and enterprise clients. Our AWS infrastructure support covers everything from multi-account setup to ongoing policy management. We also offer a structured AWS Well-Architected review to identify gaps in your current setup, and our AWS security consulting team ensures your controls align with PCI DSS, SOX, and other compliance requirements. Let us help you build a governance foundation that scales with your business.
Frequently asked questions
What are the key components of AWS governance?
Organizations, SCPs, Control Tower, and Config are the core governance tools, covering account structure, permission boundaries, automated guardrails, and continuous resource monitoring.
How do Service Control Policies (SCPs) work in AWS governance?
SCPs define maximum permissions, intersecting with IAM and resource policies to set the outer boundary of what actions an account or OU can perform, without granting access on their own.
Should startups use AWS Control Tower or manual AWS Organizations setup?
Control Tower provides a prescriptive approach that gets startups to a secure baseline quickly, while Organizations allows the fine-grained customization that larger enterprises typically need.
How can governance help with AWS compliance requirements?
Audit Manager and proactive guardrails enable compliance automation by continuously collecting evidence and enforcing controls aligned to standards like PCI DSS and SOX.