TL;DR:
- Cloud-native DevOps integrates cloud platforms, automation, and shared ownership for scalable, resilient systems.
- Key metrics like deployment frequency and MTTR guide effective continuous delivery and safety.
- Successful adoption depends on culture change, automation, environment management, and ongoing team education.
Most engineering teams think cloud-native DevOps means moving workloads to AWS or swapping Jenkins for GitHub Actions. That assumption is expensive. True cloud-native DevOps rewires how your entire organization builds, ships, and operates software. The delivery speed and cost efficiency gains are real, but they require more than a new tool stack. This guide breaks down what cloud-native DevOps actually is, how it works in practice, what metrics you should track, and where most teams quietly fail. If you are a CTO or engineering leader evaluating your next move, this is built for you.
Table of Contents
- What is cloud-native DevOps?
- Core components and workflows of cloud-native DevOps
- Measuring cloud-native DevOps efficiency: Metrics and real-world results
- Common pitfalls and best practices for successful adoption
- Why most cloud-native DevOps rollouts fail—and what actually works
- Next steps: Get expert support for cloud-native DevOps
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Cloud-native DevOps defined | Success relies on cloud-native platforms, automation, and a culture of team ownership—not just new tools. |
| Measurable efficiency gains | Adopting cloud-native DevOps can boost deployment speed 10x and reduce infrastructure costs by up to 87 percent. |
| Automation and workflows | Automation, GitOps, and secrets management are key to scalable, resilient operations in cloud-native DevOps. |
| Pitfalls and best practices | Cultural resistance, environment drift, and over-provisioning are common hurdles but can be overcome with strong team ownership and targeted optimization. |
What is cloud-native DevOps?
Cloud-native DevOps is the practice of combining cloud-native platforms, such as Kubernetes, microservices, and managed services, with DevOps principles like automation, shared ownership, and continuous delivery. The result is a system designed to scale, self-heal, and ship fast by default rather than as an exception.
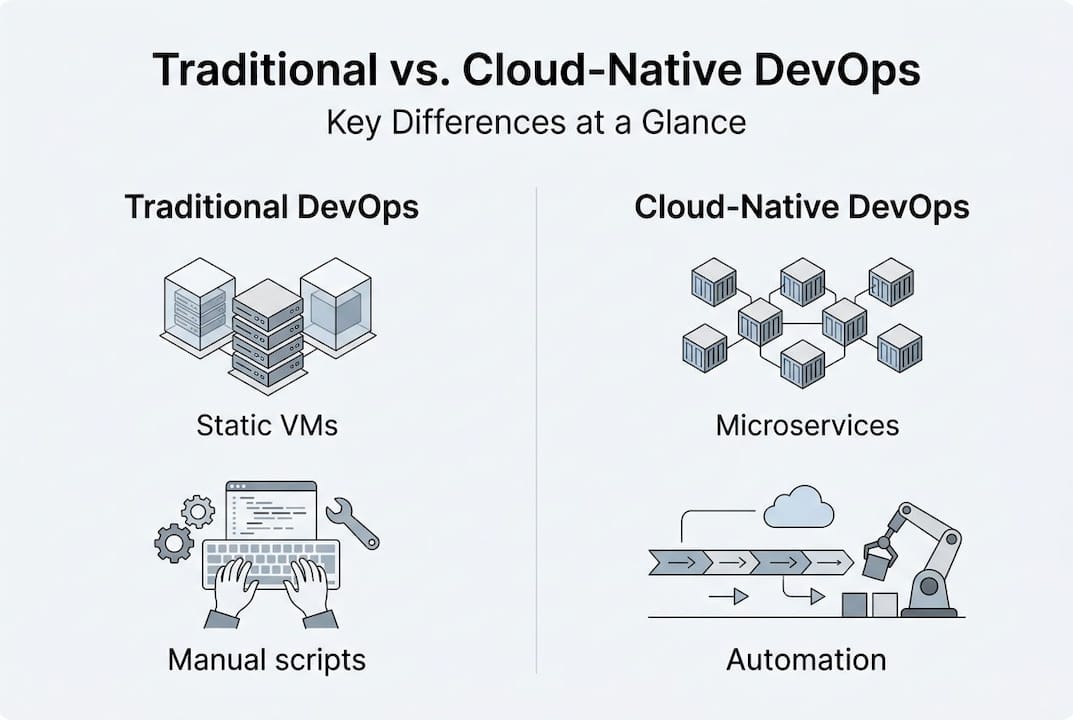
This is not the same as a traditional DevOps setup. Legacy DevOps often runs on static virtual machines, relies on scripted deployments, and keeps ops teams separate from developers. Traditional DevOps vs. cloud-native approaches look similar on the surface but diverge sharply in how teams respond to failure, scale services, and own production.
| Dimension | Traditional DevOps | Cloud-native DevOps |
|---|---|---|
| Infrastructure | Static VMs, manual provisioning | Dynamic containers, auto-scaling |
| Deployment model | Scheduled releases | Continuous, on-demand deploys |
| Team ownership | Siloed dev and ops | “You build it, you run it” |
| Resilience | Manual recovery | Self-healing, automated rollback |
| Cost model | Fixed capacity | Pay-per-use, right-sized |
Lift-and-shift migration, where you copy existing servers into the cloud unchanged, is not cloud-native transformation. Cloud-native transformation requires flexible infrastructure, automation, and a culture shift. Tools alone do not create that shift.
The core principles driving cloud-native DevOps include:
- Automation first: Every repeatable task from testing to provisioning runs automatically.
- Self-service infrastructure: Developers provision and manage their own environments without waiting for ops tickets.
- Resilience by design: Systems expect failure and recover without human intervention.
- Shared ownership: The team that writes the code also monitors and maintains it in production.
- Incremental delivery: Small, frequent releases reduce blast radius and speed up learning.
Browse DevOps insights to see how these principles apply across industries. And if you are weighing platform options, a detailed look at AWS competitors in cloud-native DevOps can help frame your decision.
Culture is the hardest part. Teams that focus purely on tooling miss the fact that a Kubernetes cluster managed by a siloed ops team is still a siloed ops team. The platform changes. The habits do not. That gap is where most transformations stall.
Core components and workflows of cloud-native DevOps
Understanding the principles is one thing. Knowing what cloud-native DevOps looks like on a Tuesday afternoon is another. Here are the foundational building blocks.
CI/CD pipelines are the operational spine. Every code commit triggers automated build, test, security scan, and deployment steps. No manual handoffs, no “works on my machine” releases. Review CI/CD best practices to see how high-performing teams structure these pipelines for reliability and speed.
GitOps takes this further by treating Git as the single source of truth for infrastructure state. All environment configuration lives in version-controlled repositories. Tools like ArgoCD and Flux watch those repos and reconcile cluster state automatically. Multi-cluster management, secret handling, and drift detection are where GitOps gets nuanced. ArgoCD ApplicationSets handle hub-spoke models across environments, while Flux works well for per-cluster setups.
Secret management is non-negotiable for security and compliance. Storing credentials in plaintext inside Git repositories is a critical vulnerability. Tools like Sealed Secrets and SOPS encrypt secrets before they enter version control, keeping your pipelines clean without sacrificing automation.
| Component | Tool examples | Primary function |
|---|---|---|
| CI/CD pipeline | GitHub Actions, GitLab CI | Automate build, test, deploy |
| GitOps engine | ArgoCD, Flux | Reconcile desired vs. actual state |
| Secret management | Sealed Secrets, SOPS | Encrypt credentials in Git |
| Drift detection | Kubecost, Crossplane | Alert and auto-correct config drift |
| Observability | Prometheus, Grafana | Track performance and reliability |
Here is a simplified workflow from code commit to production:
- Developer pushes code to a feature branch in Git.
- CI pipeline triggers: unit tests, integration tests, container image build.
- Security scanner checks the image for known vulnerabilities.
- Merge to main branch updates the GitOps repository with the new image tag.
- ArgoCD or Flux detects the change and applies it to the target cluster.
- Canary or blue-green deployment routes a small percentage of traffic to the new version.
- Monitoring checks error rates and latency. Automated rollback fires if thresholds are breached.
- Full traffic shift completes after the soak period passes.
Pro Tip: Set up drift detection alerts before you need them. Teams that discover environment drift during an incident spend 3x longer resolving it than those with proactive alerts already in place.
Explore AWS automation workflows for a practical breakdown of how these steps map to AWS-native tooling like CodePipeline and EKS.
Measuring cloud-native DevOps efficiency: Metrics and real-world results
If you cannot measure it, you cannot improve it. The DORA metrics framework (developed by Google’s DevOps Research and Assessment team) gives engineering leaders four specific signals to track.
- Deployment frequency: How often does your team ship to production?
- Lead time for changes: How long from code commit to running in production?
- Mean time to recovery (MTTR): How fast do you restore service after an incident?
- Change failure rate: What percentage of deployments cause degradation or rollback?
Elite DevOps teams deploy on demand (multiple times daily), achieve lead times under one day, recover from incidents in under an hour, and keep change failure rates below 5%. These numbers are not aspirational. They are reproducible with the right architecture.
Real-world fintech benchmarks make this concrete. One cloud-native team cut deployment time from 3 days to 15 minutes, achieved 45% AWS cost savings, and reduced their Kubernetes bill by 87% through rightsizing and workload scheduling. Those numbers shift the business case significantly.
“Deployment frequency and lead time are lagging indicators. MTTR and change failure rate tell you whether your system is actually getting safer over time.”
For engineering leaders, the practical benchmarking approach looks like this:
- Baseline your current DORA metrics before any transformation begins.
- Set 90-day targets for each metric tied to specific architectural changes.
- Track agility and cost savings together, not separately. Speed that increases your cloud bill is not a win.
- Use change failure rate as your primary safety signal. Teams optimizing only for speed often see this metric spike.
Learn more about faster software delivery and how pipeline architecture directly influences lead time. For infrastructure spend, cloud cost reduction strategies offer specific levers you can pull in parallel with your DevOps transformation.
Common pitfalls and best practices for successful adoption
The numbers from elite teams look compelling. The path to get there is less clean. Here is what actually blocks progress.
Culture resistance is the first wall. Engineers resist “you build it, you run it” because it expands their on-call burden without (at first) expanding their autonomy. Leaders resist it because it blurs accountability lines they rely on for incident management. Culture resistance, environment drift, and over-provisioning are consistently ranked as the top blockers in cloud-native adoption surveys. Average resource utilization across enterprise cloud environments sits between 32% and 41%, meaning teams are paying for capacity they never use.
Common adoption pitfalls include:
- Superficial rebranding: Renaming your IT ops team “DevOps” without changing workflows or incentives.
- Environment drift: Manually patching staging but not updating the GitOps repo, causing production surprises.
- Security gaps: Storing secrets in environment variables or plaintext config files to “save time.”
- Over-provisioning: Sizing clusters for peak load without auto-scaling policies, burning budget on idle compute.
- Ignoring saturation metrics: Tracking only CPU and memory, missing network and disk I/O bottlenecks.
“Ownership is not a personality trait. It is a system design choice. Build the incentives and tooling for it, and behavior follows.”
Pro Tip: Run a quarterly rightsizing review using your cloud provider’s cost explorer. Teams that automate this process catch over-provisioning before it compounds across multiple environments.
Best practices that actually hold up:
- Automate rightsizing recommendations and act on them on a regular cadence.
- Use tagging policies to track cost by team, service, and environment.
- Enforce security in the pipeline (shift left) rather than auditing after the fact.
- Monitor utilization, not just uptime. Availability SLAs do not catch silent waste.
For cost-focused strategies, cloud cost optimization covers the full playbook. Teams in high-transaction sectors can also explore AWS in DevOps for retail or DevOps for e-commerce for industry-specific patterns.
Why most cloud-native DevOps rollouts fail—and what actually works
After 700+ projects across fintech, retail, and enterprise, the pattern is clear. Teams that fail are usually not missing the right tools. They are missing alignment between engineering incentives and operational outcomes.
The “you build it, you run it” model is more disruptive than most CTOs anticipate. It forces product and engineering teams to confront the real cost of complexity, because they now own it in production. That is uncomfortable. It is also exactly why it works.
Superficial cloud-native rebranding, spinning up Kubernetes without rethinking how teams interact with infrastructure, adds ops complexity without delivering speed. We have seen it repeatedly. The teams that sustain transformation share three habits: they set a clear platform vision, invest in ongoing education (not just initial training), and celebrate incremental wins rather than waiting for a big-bang cutover.
DevOps in cloud agility is not an end state. It is a feedback loop. The organizations winning right now treat it that way.
Next steps: Get expert support for cloud-native DevOps
The gap between knowing what cloud-native DevOps requires and actually operating it at scale is where most teams lose momentum. Infrastructure decisions made under pressure without deep AWS expertise tend to compound into technical debt fast.
IT-Magic has been delivering cloud infrastructure and DevOps transformations since 2010, with 700+ projects for fintech, startup, and enterprise clients. Our certified AWS engineers design and operate the pipelines, Kubernetes clusters, and automation workflows covered in this guide. If you are ready to accelerate delivery without adding operational risk, explore our AWS infrastructure support and Kubernetes support services to see how we can help your team move faster and spend less.
Frequently asked questions
How is cloud-native DevOps different from traditional DevOps?
Cloud-native DevOps uses microservices, containers, dynamic orchestration, and full automation, while traditional DevOps typically relies on static infrastructure and manual deployment steps. Cloud-native requires flexible infrastructure and automation at every layer, not just a change in tooling.
What metrics define successful cloud-native DevOps teams?
Key metrics include deployment frequency, change lead time, MTTR, and change failure rate. DORA metrics benchmarks show elite teams deploying multiple times daily and resolving incidents within an hour.
What are common challenges with cloud-native DevOps?
Resistance to culture change, environment drift, security gaps from poor secrets management, and resource over-provisioning are the most frequent blockers. Culture resistance and over-provisioning both require deliberate process changes, not just new tooling.
How does GitOps streamline cloud-native DevOps?
GitOps manages all infrastructure state in version-controlled repositories, enabling automated compliance checks and rapid rollbacks. Hub-spoke GitOps models using ArgoCD ApplicationSets or per-cluster Flux handle multi-environment deployments at scale with encrypted secret management.
Recommended
- DevOps in cloud: drive agility and 72% cost savings
- AWS DevOps explained: accelerate delivery and scale securely
- Cloud cost optimization strategies for CIOs: a practical guide
- CI/CD in DevOps: 127x Faster Software Delivery