TL;DR:
- AWS DevOps is a continuous culture focusing on automation, collaboration, and measurable delivery improvement.
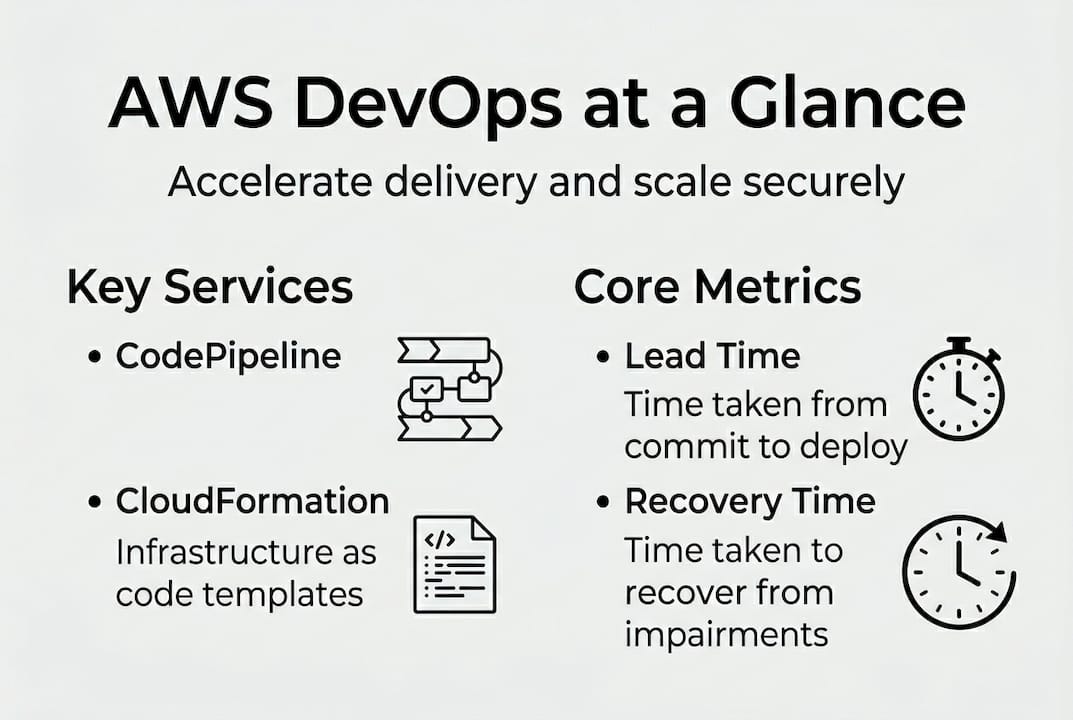
- Essential AWS tools include CodePipeline, CodeBuild, CloudFormation, ECS/EKS, and CloudWatch for streamlined workflows.
- Successful adoption relies on process, security embedding, organizational alignment, and measuring key performance metrics.
Most engineering leaders assume AWS DevOps is simply a matter of choosing the right AWS tools. That assumption costs teams months of rework and leaves real business value on the table. AWS DevOps is a set of AWS services, tools, and best practices for implementing DevOps methodologies on cloud infrastructure, enabling faster software delivery through automation, collaboration, and continuous improvement. Whether you are scaling a startup or modernizing a large enterprise, this guide covers what AWS DevOps actually means, the key service categories, best practices, and how to measure real progress.
Table of Contents
- What is AWS DevOps? Core principles and benefits
- Essential AWS DevOps services, tools, and workflows
- Best practices and advanced patterns for AWS DevOps
- Organizational impact and measuring success
- Our perspective: What most AWS DevOps rollouts miss
- Next steps: How IT-Magic can accelerate your AWS DevOps journey
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Cloud-native DevOps defined | AWS DevOps centers on using AWS services and best practices to enable fast, secure, and automated delivery pipelines. |
| Critical AWS tools | CodePipeline, CodeBuild, CloudFormation, and CloudWatch form the backbone of AWS DevOps workflows. |
| Best practices matter | Incorporate security, manual gates, and cost optimization techniques to avoid common scaling pitfalls. |
| Team structure impacts success | Separate teams that collaborate closely often drive better deployment frequency and resilience. |
What is AWS DevOps? Core principles and benefits
DevOps is not a tool or a job title. It is a culture and a practice that aligns development and operations teams around a shared goal: delivering value to users continuously, safely, and quickly. On AWS, that philosophy becomes tangible through a managed ecosystem of services, automation patterns, and documented guidance.
“The AWS Well-Architected DevOps Guidance defines DevOps through DevOps Sagas, core domains like software delivery processes, with capabilities, best practice indicators, metrics, and anti-patterns for high-velocity, secure operations at cloud scale.”
Think of the DevOps Sagas as field-tested playbooks. Each Saga covers a domain such as continuous integration, security, or reliability, and provides concrete indicators of maturity. That is a sharper framework than most organizations build on their own.
For CTOs and engineering leads, the business case is grounded in measurable outcomes. Teams that adopt AWS DevOps well typically see:
- Faster release cycles: Automated pipelines eliminate manual handoffs, cutting release times from weeks to hours.
- Higher deployment frequency: Small, frequent changes reduce risk and make debugging faster.
- Reduced incident rates: Automated testing and IaC reduce human error, a leading cause of production failures.
- Faster recovery (MTTR): Observability tooling and runbooks shrink mean time to recovery when incidents do happen.
- Better cross-team alignment: Shared pipelines and monitoring create a common operational language between Dev and Ops.
Those are not aspirational claims. They map directly to DORA metrics, the industry-standard framework for measuring software delivery performance. A well-structured DevOps automation workflow on AWS puts those metrics within reach for teams of almost any size. Security also improves dramatically when AWS cloud security strategies are embedded into pipelines from the start rather than bolted on later.
The key mental shift here: AWS DevOps is not a project you finish. It is a continuous feedback loop between delivery speed and operational stability.
Essential AWS DevOps services, tools, and workflows
With the philosophy clear, the next question is practical: which AWS services do you actually need, and how do they fit together? The AWS DevOps toolkit covers CI/CD, IaC, microservices with ECS/EKS, monitoring with CloudWatch, and SDLC automation. Here is how the core services map to real functions:
| Service | Primary purpose | Best fit |
|---|---|---|
| AWS CodePipeline | Orchestrates CI/CD workflow end to end | All team sizes |
| AWS CodeBuild | Runs build and test stages in the pipeline | Small to large teams |
| AWS CodeDeploy | Automates application deployments to EC2, ECS, Lambda | Mid to large teams |
| AWS CloudFormation | Provisions and manages infrastructure as code | All team sizes |
| Amazon ECS / EKS | Runs containerized workloads at scale | Growth stage and enterprise |
| Amazon CloudWatch | Monitors metrics, logs, and alarms | All team sizes |
These services do not operate in isolation. A typical workflow for a new project looks like this:
- Define infrastructure as code. Use CloudFormation or AWS CDK to version and deploy every resource. This makes environments reproducible and auditable.
- Build CI/CD pipelines. Wire CodePipeline, CodeBuild, and CodeDeploy together so every commit triggers automated testing and staged deployment.
- Containerize workloads. Use ECS for simpler container orchestration or EKS for Kubernetes-native setups. Both integrate cleanly with the pipeline.
- Set up monitoring and alerting. CloudWatch dashboards and alarms give you visibility before users report problems. Connect to AWS Security Hub for compliance signals.
- Iterate and optimize. Use pipeline metrics and CloudWatch data to identify bottlenecks, then refine. Check the DevOps workflow guide for practical patterns.
Pro Tip: Embed AWS security best practices and cost tagging from day one. Retrofitting security policies and cost allocation tags into a mature pipeline is painful and error-prone. Starting clean takes an hour; cleaning up later can take weeks. Industries like retail on AWS have learned this the hard way when traffic spikes expose gaps in both cost controls and security posture.
Best practices and advanced patterns for AWS DevOps
Once your baseline pipeline is running, the gap between a functional setup and a production-grade one comes down to the patterns you adopt. Here is what separates reliable teams from reactive ones:
| Pattern | Primary benefit | Key risk if skipped |
|---|---|---|
| Blue/green deployments | Zero-downtime releases | User-facing errors during updates |
| Canary releases | Gradual risk exposure | Full blast radius on bad releases |
| Manual approval gates | Human check before prod | Accidental prod deployments |
| IaC scanning (e.g., Checkov) | Catches misconfigurations early | Compliance failures and breaches |
| Graviton CPU adoption | Up to 35% EKS cost savings | Unnecessary compute spend |
Let’s unpack the ones that get overlooked most often.
Blue/green deployments keep two identical production environments running. Traffic flips from old to new only after health checks pass. Rollback takes seconds, not minutes. Most teams understand this in theory but skip it because it feels expensive. In practice, the cost of one bad deployment outweighs months of extra environment costs.
Manual approval gates in CodePipeline add a human decision point before changes hit production. This is not bureaucracy. It is a safety net that catches the edge cases automated tests miss, and it creates a clear audit trail for regulated industries.
IaC scanning with tools like Checkov runs static analysis against your CloudFormation or Terraform templates before they ever reach AWS. It catches overly permissive IAM policies, open security group rules, and missing encryption settings. Embedding this into the pipeline means security review happens at commit time, not during a quarterly audit. Pair this with AWS DevOps security practices for a layered defense.
Pro Tip: Schedule a blameless incident review meeting after every production issue, even minor ones. Teams that do this consistently cut repeat incidents by identifying process gaps rather than blaming individuals. It also accelerates the cultural shift that makes DevOps sustainable long-term. This is equally critical whether you are managing cloud security strategies for fintech or e-commerce.
Organizational impact and measuring success
AWS DevOps changes more than your pipeline. It reshapes how teams are organized, how work flows between them, and what leaders measure. Getting this part right is often harder than the technical implementation.
On the structural side, there is a persistent debate: should Dev and Ops be separate teams with strong collaboration, or should engineers be fully embedded? Research published in Frontiers in Computer Science found that separate Dev and Ops teams with high collaboration outperform fully embedded teams on deployment frequency and incident rates. Full embedding creates ownership confusion. Separate teams with clear handoffs and shared tooling tend to move faster.
To measure progress, use the DORA and SPACE frameworks as your north star. Track these signals:
- Deployment frequency: How often you ship to production
- Lead time for changes: Time from code commit to production
- Change failure rate: Percentage of deployments causing incidents
- Mean time to recovery (MTTR): How fast you restore service after failure
- Developer satisfaction: A SPACE metric that predicts long-term team health
The Well-Architected DevOps Guidance recommends starting with AWS Code services and prioritizing IaC, monitoring, and left-shifted security before optimizing team structure. That sequence matters. Teams that chase org chart changes before their pipelines are stable tend to stall.
Fostering continuous improvement also means building learning rituals: regular retrospectives, shared runbooks, and rotation programs that give developers operational context. If you are evaluating AWS against competitor platforms for your stack, these organizational factors matter as much as feature parity. Teams running DevOps for e-commerce know that culture debt compounds just like technical debt.
Our perspective: What most AWS DevOps rollouts miss
After 700+ projects across startups, fintech, and enterprise clients, we have seen a clear pattern: teams over-invest in tool selection and under-invest in process design and cultural buy-in. The tools are the easy part. AWS gives you everything you need. What fails is the organizational muscle to use those tools consistently under pressure.
The second most overlooked area is security and compliance at cloud scale. Most teams add security checks after the pipeline is built. By then, patterns are set, habits are formed, and retrofitting is painful. Left-shifted security is not optional in regulated industries. It is the foundation.
Finally, teams skip continuous measurement. They launch a pipeline, call it done, and never revisit the DORA metrics. Without feedback loops, pipelines drift and quality erodes. Our advice: start small, measure from day one, get cross-functional buy-in before the first sprint, and evolve your structure as scale demands. Our AWS DevOps consulting insights reflect this hard-won approach.
Next steps: How IT-Magic can accelerate your AWS DevOps journey
Building a production-grade AWS DevOps practice takes more than documentation. It takes proven patterns, hands-on configuration, and someone who has seen what breaks at scale.
At IT-Magic, our certified AWS engineers have delivered AWS DevOps services across startups, fintech, and enterprise environments since 2010. We start most engagements with an AWS Well-Architected Review to identify gaps before they become incidents. From there, we build or optimize your pipelines, harden your security posture, and provide ongoing AWS infrastructure support so your team can focus on shipping. Whether you are starting from scratch or scaling an existing setup, we work as your dedicated cloud and DevOps partner, not just a vendor.
Frequently asked questions
What makes AWS DevOps different from traditional DevOps?
AWS DevOps leverages native cloud services to automate infrastructure, deployment, and monitoring, integrating AWS best practices for scale and reliability that general DevOps toolchains require you to assemble manually.
Which AWS services are essential for starting DevOps?
Key AWS DevOps services include CodePipeline, CodeBuild, CodeDeploy, CloudFormation, EKS, ECS, and CloudWatch, which together cover CI/CD, IaC, and monitoring for modern workflows.
How do organizations measure AWS DevOps success?
Success is measured with DORA or SPACE metrics such as deployment frequency, lead time, and mean time to recovery, where DevOps adoption improves MTTR across team structures.
What team structures work best for AWS DevOps adoption?
Separate Dev and Ops teams with strong collaboration typically outperform fully embedded models on deployment frequency and incident rates, making clear ownership with shared tooling the recommended starting point.
Recommended
- Build a robust DevOps automation workflow in AWS
- AWS DevOps Services | IT-Magic
- Cloud Infrastructure Explained: Scale, Secure, Optimize AWS
- CI/CD in DevOps: 127x Faster Software Delivery